Top 7 Techniques for Identifying Throwaway Domains
Throwaway domains, also known as disposable email addresses, are temporary emails often used to bypass signup requirements. While they might seem harmless, they pose serious risks for businesses, such as fake accounts, increased bounce rates, and potential fraud. Identifying these domains is critical to maintaining clean email lists, reducing costs, and protecting your platform from abuse.
Here are the 7 best ways to detect throwaway domains:
- TempMailChecker API: Tracks over 277,938 disposable domains, offers real-time detection, and integrates easily with various programming languages.
- DNS MX Record Checks: Verifies a domain's mail server setup to flag suspicious or poorly configured domains.
- Domain Blacklist Matching: Compares domains against databases of known temporary email providers.
- Regex Pattern Analysis: Identifies emails with suspicious patterns, like random alphanumeric usernames or known disposable domain structures.
- Domain Age Verification: Flags newly registered domains often used for temporary purposes.
- Behavioral Risk Scoring: Analyzes user behavior, like registration speed or lack of social media presence, to identify fake accounts.
- Reverse Email Lookup: Checks if an email is tied to legitimate online profiles or appears in data breaches.
Combining these methods ensures a layered approach to detecting and blocking throwaway domains, safeguarding your platform and improving data quality.
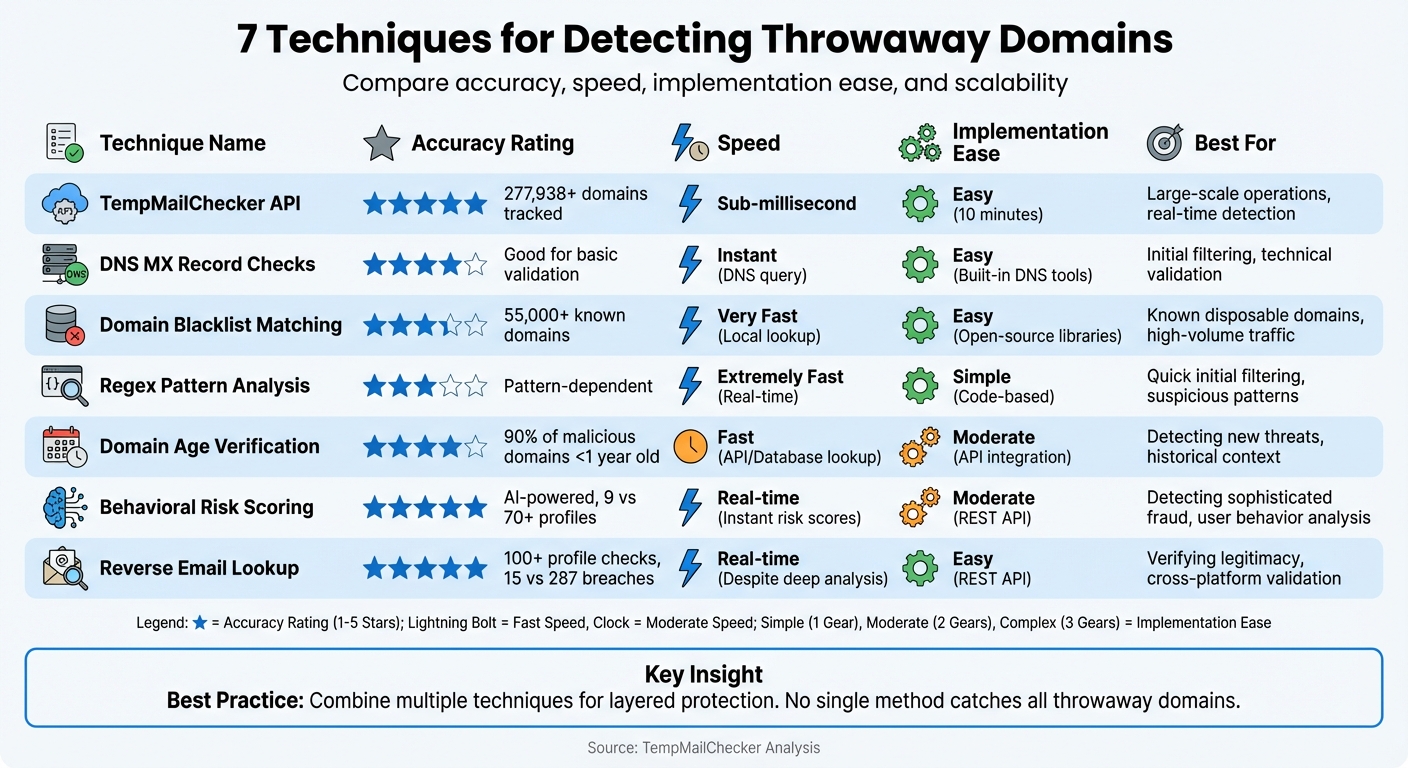
Comparison of 7 Throwaway Domain Detection Techniques: Accuracy, Speed, and Scalability
1. TempMailChecker API Integration
Accuracy in Detecting Disposable Domains
TempMailChecker's API takes detection to the next level by going beyond simple blacklists. Its database tracks over 277,938 disposable domains and is updated daily to keep pace with new temporary email services. This ensures broad and up-to-date coverage.
The system performs in-depth checks, including validating MX records, testing SMTP servers, and analyzing domain age - flagging domains registered within just four days. It also uses Open Source Intelligence (OSINT) to determine if an email has been blacklisted by third-party services, such as social media platforms.
Speed and Efficiency of Detection
TempMailChecker isn’t just accurate - it’s fast. When validating emails during signups, speed is critical. The API processes requests in sub-millisecond time, delivering results instantly as users type their email addresses. Compare this to manual blacklist checks, which often take 20 to 40 seconds, and the advantage is clear.
This efficiency is powered by consolidated metadata. A single API call performs multiple verifications simultaneously, eliminating the need for juggling multiple tools or waiting for sequential checks to finish.
Ease of Implementation or Integration
Getting started with TempMailChecker is quick and straightforward - it takes just 10 minutes to integrate. The REST API supports a wide range of programming languages, including NodeJS, PHP, Python, Ruby, Rust, Elixir, Clojure, and Go. The service provides a simple JSON response that indicates whether an email is disposable, making it easy to incorporate into any signup process.
You can begin with a free plan that includes 25 daily requests. For higher usage, paid plans start at $12 per month, with enterprise-level options available for larger needs.
Ability to Handle Large-Scale Operations
For businesses managing thousands of signups daily, TempMailChecker offers regional endpoints to reduce latency and priority API routing for paid plans. The Growth plan, priced at $29 per month, supports 15,000 requests per month with higher burst limits. Meanwhile, the Scale plan, at $69 per month, handles up to 60,000 requests with dedicated throughput - perfect for e-commerce platforms and industries with high security demands.
With automated database updates, there’s no need to maintain your own blocklists. This hands-off approach allows your team to focus on what matters most: your core business operations.
sbb-itb-cfbd9fd
2. DNS MX Record Checks
Accuracy in Detecting Disposable Domains
By integrating a reliable API, verifying MX records provides a clear view of a domain's email setup. DNS MX checks focus on a domain's mail server infrastructure to determine its legitimacy.
Legitimate email providers typically maintain well-configured mail servers. In contrast, many disposable email domains either lack valid MX records or rely on minimal setups. This makes MX checks a useful tool for identifying low-quality, temporary email services. Understanding how temporary email addresses work is essential for building effective defenses. However, some advanced disposable services may use legitimate-looking MX records to bypass detection.
Speed and Efficiency of Detection
Once the domain structure is confirmed, speed becomes crucial for real-time detection. MX record checks query DNS servers instantly, making them a quick verification step during the signup process. This approach ensures even newly created disposable domains can be identified promptly.
"MX records tell you which mail servers handle emails for a domain. Looking at these records helps figure out if a domain's got a legit email setup, which can be handy for spotting disposable email domains." – Robert Chen, Frontend Developer & UX Specialist
Ease of Implementation or Integration
For developers, implementing MX record checks is a straightforward process. It starts with extracting the domain from a user's email address and performing a DNS lookup for its MX records. Many programming environments come equipped with DNS toolkits, simplifying integration.
Using MX validation as an initial filter during signup can help block domains incapable of receiving emails. Domains with minimal MX configurations or mismatched forward/reverse DNS settings often signal low integrity. Pairing MX checks with blacklist and regex analyses creates a more thorough filtering system. This combined approach enhances detection capabilities and strengthens overall email verification efforts.
How Does Email Validation Detect Temporary Email Addresses? - TheEmailToolbox.com
3. Domain Blacklist Matching
In addition to technical checks like DNS MX and domain age verification, blacklist matching serves as a practical way to flag known disposable email domains.
Accuracy in Detecting Disposable Domains
Blacklist matching works by comparing incoming email domains against extensive databases of known temporary email providers. For instance, one open-source library maintains a database of over 55,000 disposable email providers. These lists are often curated by communities and third-party services.
The accuracy of this method depends largely on how up-to-date and thorough the blacklist is. While it’s effective at identifying established disposable domains, it struggles with newly created domains that haven’t yet been added to the lists. Real-time APIs, rather than static lists, can address this gap by catching emerging disposable domains before they are widely used.
"These lists are often incomplete or outdated, with updates typically occurring every few weeks. They lack professional verification because they depend on volunteers to submit new domains." – UserCheck
Speed and Efficiency of Detection
Blacklist matching is incredibly fast, relying on string comparisons or hash table lookups for instant validation. When implemented locally, it avoids the delays caused by external API calls. This makes it particularly useful for real-time validation during user registration to block disposable emails at signup, offering a speed advantage over many other methods.
Ease of Implementation or Integration
Developers will find blacklist matching relatively simple to set up. Open-source libraries are available for various programming languages, including NodeJS, Python, PHP, Ruby, and Go. Client-side checks using JavaScript can provide immediate feedback before form submission, reducing the load on servers. To ensure accuracy, automate the process of updating blacklists by scheduling scripts to fetch the latest versions from community repositories. For a more comprehensive approach, combine blacklist matching with MX record checks and domain age verification to detect both known and suspicious new domains.
Ability to Handle Large-Scale Operations
Blacklist matching is well-suited for platforms handling high volumes of traffic. By storing blacklists in a hash set, detection speed remains constant regardless of the number of domains being checked. This makes it an efficient choice for systems processing thousands of signups daily.
| Method | Speed | Accuracy | Maintenance | Cost |
|---|---|---|---|---|
| Static Blacklist | Very Fast (Local) | High for known domains | Manual/Scheduled updates | Free (Open-source) |
| Real-Time API | Slower (Network Latency) | High (includes new domains) | Automatic | Usage-based |
This table highlights the trade-offs between static blacklists and real-time APIs in disposable domain detection. Additionally, monitoring when users attempt to switch their recovery email to a blacklisted domain can help identify potential fraudulent activity.
4. Email Pattern Analysis Using Regex
Regex helps identify disposable emails by spotting known patterns. It works as a quick, lightweight tool to catch suspicious emails right at the signup stage, complementing other verification methods.
Accuracy in Detecting Disposable Domains
Regex is particularly good at recognizing common naming styles used by temporary email services. For example, it can flag emails with long, random alphanumeric usernames or domains like .*@mailinator\.com. However, it’s not foolproof. Legitimate users with similar email formats might get flagged, and some disposable services use domains that mimic legitimate ones to bypass basic pattern detection.
"By crafting regex patterns, you can flag such emails to strengthen your verification process" – Robert Chen, Frontend Developer & UX Specialist, Mail7.
When paired with tools like the TempMailChecker API, regex can significantly reduce fraudulent signups.
Speed and Efficiency of Detection
Regex validation works almost instantly, making it a great choice for real-time checks during user registration. Its local pattern-matching capabilities allow for immediate results without the need for network requests.
Ease of Implementation or Integration
Regex is a developer-friendly solution that works with nearly all programming languages, including NodeJS, Python, PHP, Ruby, and Go. It can be implemented on the client side using JavaScript for instant user feedback, while server-side validation ensures data integrity.
That said, regex patterns need regular updates to keep up with evolving throwaway email formats. Instead of hardcoding rules, developers might consider using an updated repository or combining regex with other techniques to improve detection accuracy.
Ability to Handle Large-Scale Operations
For high-traffic platforms, regex-based checks are a practical choice. They are computationally efficient, enabling the system to process thousands of registrations per second. By using regex as a quick initial filter, obvious disposable emails can be flagged before moving on to more resource-intensive methods, like MX record checks. This layered approach balances speed and cost-effectiveness.
| Feature | Regex Pattern Analysis | API/Database Lookup |
|---|---|---|
| Detection Speed | Extremely High (Real-time) | Moderate (Network Latency) |
| Implementation | Simple (Code-based) | Moderate (Requires Integration) |
| Maintenance | High (Manual updates needed) | Low (Managed by provider) |
| Accuracy | Moderate (Pattern-dependent) | High (Database-dependent) |
| Scalability | High (No per-call cost) | High (But may incur API costs) |
5. Domain Age and WHOIS Verification
Domain age is a reliable indicator for spotting throwaway email domains. Studies show that around 90% of domains listed in malicious blacklists were registered within a year of their detection. Fraudsters often use newly registered domains to evade blacklists, discarding them once flagged. By incorporating domain age into validation processes, you add a layer of historical context to technical checks, enhancing the overall analysis.
Accuracy in Detecting Disposable Domains
Beyond technical validations like MX record checks and regex analysis, domain age adds an essential lens for assessing legitimacy. It helps identify threats from newly registered domains before they even appear on blacklists. For instance, domains registered within the last 30 days are considered high-risk. This additional layer of verification strengthens multi-tiered detection systems.
"A brand-new, inactive email? That's kinda suspicious. You wanna look for emails that have been around and are used regularly." – Robert Chen, Frontend Developer & UX Specialist.
Speed and Efficiency of Detection
Performing direct WHOIS queries for real-time checks is impractical due to rate limits. Instead, pre-compiled databases or Domain Age APIs can provide instant access to registration dates. For large-scale operations, bulk processing through updates from TLD zone files is a more efficient way to handle millions of domains.
Ease of Implementation and Integration
Developers can easily incorporate domain age verification using REST APIs that return the registration date and calculate the domain's age in days, months, or years. However, WHOIS data often varies in format across registrars, making automated processing a challenge. For high-volume systems, accessing TLD zone files, such as those provided by Verisign's Zone File Access program, offers a scalable alternative to individual WHOIS lookups.
Handling Large-Scale Operations
Managing large-scale domain data is crucial when dealing with high-volume systems. For example, the ".com" TLD alone includes approximately 112 million domains, with around 110,000 new registrations and 72,000 deletions occurring daily. Running WHOIS queries for every email address would overwhelm most systems. Instead, downloading daily zone file updates allows for bulk tracking of new registrations, bypassing the limitations of direct WHOIS queries. Incorporating domain history into these processes further bolsters the multi-layered approach to detecting disposable emails.
6. Behavioral Risk Scoring
Behavioral risk scoring takes a closer look at how users behave during and after signing up, focusing on metrics like registration speed and patterns in online activity. For instance, if multiple accounts are created from the same IP address within minutes or an email address shows no presence on social media, these could be warning signs of disposable email usage. This method goes beyond technical checks by diving into the actual behavior of users.
This approach uses AI-powered models to distinguish real users from temporary or suspicious accounts. A key metric here is "Online Velocity", which measures the number of social profiles tied to an email. Legitimate emails usually connect to around nine platforms, while questionable ones might link to over 70. Another useful metric is verifying "Name Consistency" across platforms like Google, Airbnb, and Skype, which can signal trustworthiness.
Accuracy in Detecting Disposable Domains
Behavioral scoring shines in spotting issues that traditional methods might overlook. For example, it can detect tricks like Gmail aliasing, where users manipulate addresses by adding dots (e.g., e.x.am.p.le@gmail.com). It also flags emails with no social or historical activity - accounts that often indicate they were created solely for one-time use. By combining these subtle signals, the system generates a strong risk score.
"Behavioral analysis watches what users do after they sign up, using AI to guess if they're using a disposable email." – Robert Chen, Frontend Developer & UX Specialist
Speed and Efficiency of Detection
Like regex and DNS checks, behavioral scoring provides real-time insights, but it goes a step further by analyzing user actions instead of just static data. These systems return detailed risk scores in fractions of a second, allowing for instant decisions, such as requiring phone verification for medium-risk users or outright blocking high-risk accounts.
Ease of Implementation and Integration
Modern detection tools come with detailed REST APIs that integrate smoothly into existing signup processes without causing significant disruptions. Developers can add these checks with minimal coding effort, improving verification steps while maintaining a seamless user experience.
Ability to Handle Large-Scale Operations
Behavioral scoring systems are built to handle massive volumes, analyzing over a million lookups daily and processing data from more than 200 countries. With AI continuously learning from global user patterns, these systems adapt and scale effortlessly to meet the demands of large-scale operations.
7. Reverse Email Lookup
Reverse email lookup digs into the digital trail of an email address to determine if it's tied to genuine online activity. Instead of merely checking if the domain appears on a blacklist, this method investigates whether the email is associated with profiles on platforms like Google, Skype, Airbnb, or LinkedIn. On average, a legitimate email is connected to about 9 online profiles. In contrast, disposable or fake emails might show no connections or an unusually high number, such as 70+ profiles. This approach adds a behavioral layer to traditional technical checks, making it a valuable complement to other detection methods.
Accuracy in Detecting Disposable Domains
This technique goes a step further by identifying disposable emails that evade standard domain checks, relying on specific user signals. For instance, it verifies if the name associated with an email remains consistent across platforms - checking if "Matthew" on Google also appears as "Matthew" on Airbnb, rather than being listed as "Simon" elsewhere. It also examines data breach records. Legitimate emails might show up in approximately 15 breaches over the years, while fake or shared emails could appear in as many as 287 breaches. Additionally, it flags inconsistencies in location data, such as an account showing the UK on Airbnb but Nigeria on Google Maps.
Speed and Efficiency of Detection
Modern disposable email checker APIs make these checks incredibly fast, performing deep analyses in real time during user registration. Even when processing data from over 100 profiles, the system delivers instant results without slowing down the signup process. This ensures a smooth user experience while maintaining robust security.
Ease of Implementation and Integration
Reverse email lookup can be easily integrated into existing verification processes. REST APIs supporting multiple programming languages - like NodeJS, Python, PHP, and Go - allow developers to incorporate this method with minimal effort. It works seamlessly alongside other validation steps, strengthening security measures without complicating workflows.
Ability to Handle Large-Scale Operations
These systems are built to handle high-volume operations, processing thousands of emails through real-time API calls or bulk CSV uploads for database audits. With databases tracking over 55,734 fake email providers, this technology ensures reliable performance even on platforms with heavy traffic, maintaining consistent results at scale.
Conclusion
No single solution can catch every throwaway domain. Disposable email services are constantly evolving - using valid MX records and imitating trusted providers to bypass detection systems. To address this, a multi-layered approach is essential. Combining DNS verification, regex patterns, domain blacklists, and behavioral analysis provides a more accurate way to assess risks. This is especially important in industries like healthcare and finance, where even one fake account can result in serious security breaches.
Static blocklists and manual GitHub repositories fall short in keeping up with the rapid creation of disposable domains. Real-time API integration offers a better solution, automatically updating detection databases as users enter information. For example, TempMailChecker can handle over 277,938 disposable domains at lightning-fast speeds, making it ideal for high-traffic operations. One SaaS startup reported a 25% increase in valid user signups after implementing real-time email verification.
Security doesn’t stop at signup. Businesses should monitor post-login activity, particularly when users attempt to change recovery emails to throwaway domains - an often-used tactic in account takeover attacks. Strengthening your platform with tools like multi-factor authentication (MFA) and double opt-in processes adds another layer of security. These ongoing measures work hand in hand with robust signup defenses to ensure comprehensive protection.
Overlooking disposable emails can lead to broader problems. For instance, if 10% of your email list consists of throwaway addresses, your bounce rates will spike, damaging your sender reputation with providers like Gmail. This can also trigger warnings from your email service provider, jeopardizing your deliverability. To avoid these pitfalls, combining multiple detection methods is key. Regular database audits paired with real-time validation help maintain clean data and accurate analytics.
Don’t wait to secure your platform. Start by testing TempMailChecker’s free tier locally and scale up as your needs grow. Delays only allow fake accounts to accumulate, making cleanup more complicated down the line.
FAQs
What are the risks of throwaway email domains for businesses?
Throwaway email domains, also called disposable email addresses, can create significant challenges for businesses. For one, they often result in higher bounce rates, which can hurt your sender reputation. This, in turn, increases the chances of your legitimate emails being flagged as spam or outright blocked by email providers. On top of that, these domains are frequently associated with spam-trap databases, further damaging your email deliverability.
But the problems don’t stop there. Disposable email addresses are a favorite tool for cybercriminals. They’re often used to set up fake accounts, carry out phishing scams, or bypass security systems. Because these addresses are temporary and difficult to trace, they make it much harder to investigate abuse or enforce security measures effectively.
To protect your business, detecting and blocking these domains in real time is crucial. Tools like TempMailChecker can help by quickly identifying disposable email addresses. This allows you to shield your user base, improve email performance, and cut down on spam efficiently.
How can you identify a disposable email address?
Disposable email addresses often reveal themselves through a few telltale signs. One of the most obvious clues? The domain name. These domains typically belong to well-known temporary email providers, feature random combinations of letters and numbers, or look oddly long and nonsensical. Think examples like john1234@temp-mail.com or abc987xyz@randommailservice.com - both scream "disposable."
Another way to spot them is by examining the domain's DNS records, especially its MX (mail exchange) records. If a domain lacks a proper mail server or is tied directly to a throwaway email service, it's a solid red flag.
Many detection tools also rely on comparing domains against a regularly updated database of known temporary email providers. If there's a match, it's almost certain the email is temporary. Beyond that, patterns like quick one-time sign-ups or a lack of engagement - such as high bounce rates or unopened emails - can also hint at disposable email usage.
For businesses looking to tackle this issue, tools like TempMailChecker can make life easier. With its powerful API, it identifies disposable domains in real time, helping businesses block fake accounts, cut down on spam, and reduce fraud with minimal hassle.
Why is it important to use multiple methods to detect throwaway domains?
Detecting throwaway domains effectively requires using multiple methods. Disposable email providers are constantly creating new domains and finding ways to bypass single detection techniques. For instance, depending solely on DNS or MX record checks might overlook domains with hidden or customized configurations. A layered approach, combining strategies like domain blacklists, DNS lookups, and reputation analysis, provides broader and more reliable coverage.
This multi-method strategy also minimizes false positives and negatives. DNS and MX checks can uncover unusual setups, while blacklists and reputation analysis help flag domains often linked to spam, fraud, or fake signups. By merging these techniques, businesses can keep their email lists cleaner and reduce the risk of misuse.
TempMailChecker streamlines this process with a robust API. It offers real-time DNS validation, access to a vast database of over 277,938 disposable domains, and lightning-fast response times, making it a dependable tool for identifying throwaway email addresses.
