10 Best Practices for Preventing Fraudulent Registrations
Fraudulent registrations are a growing problem, costing businesses billions annually. These fake accounts, often created using stolen or synthetic identities, lead to financial losses, compliance risks, and skewed user data. To combat this, here are 10 practical strategies to identify and block fraud without disrupting genuine users:
- Block Disposable Emails: Tools like TempMailChecker detect and block temporary email addresses in real time.
- Validate Emails: Ensure emails are formatted correctly, exist, and can receive messages.
- Use CAPTCHA: Stop bots with challenges that are easy for humans but hard for scripts.
- Monitor IP Data: Check IP reputation and location for suspicious patterns.
- Track Device Fingerprints: Identify repeated attempts from the same device.
- Apply Multi-Factor Authentication (MFA): Add extra security for high-risk registrations.
- Leverage Behavioral Analytics: Spot unusual user behavior, like rapid form submissions.
- Set Rate Limits: Control the number of signups from a single source.
- Implement Risk Scoring: Assign risk levels to registrations based on multiple data points.
- Review and Update Policies: Continuously refine your system to address evolving fraud tactics.
Fraud prevention requires layering these strategies to stay ahead of attackers while maintaining a smooth experience for legitimate users. Each method plays a role in protecting businesses from the financial and operational impacts of fake registrations.
Block Fake Account Creation by Bots & Fraudsters with Forter identity Protection
1. Use TempMailChecker to Detect Disposable Emails
Disposable email addresses are a go-to tool for fraudsters looking to create fake accounts. These temporary addresses let them sidestep verification processes and register multiple accounts without leaving any trace. By blocking these emails during the signup process, you can shut down one of the most common methods used for fraudulent activity. TempMailChecker provides a fast and reliable way to tackle this issue head-on.
TempMailChecker works by identifying disposable email domains in real-time, relying on a constantly updated database of over 277,938 temporary domains. This database is refreshed daily to stay ahead of new threats. When a user submits an email during registration, the system processes it in under a millisecond, returning a simple JSON response. This lightning-fast process ensures that legitimate users aren’t inconvenienced, while fraudulent attempts are stopped immediately.
Integration is straightforward with a REST API that supports multiple programming languages. For testing purposes, a free tier is available, allowing up to 25 requests per day.
The tool operates seamlessly in the background, blocking disposable emails without interfering with genuine signups. This ensures a smooth registration experience for real users while keeping fake accounts at bay.
For platforms with heavy traffic, TempMailChecker offers scalable pricing plans, starting at $12 per month for 3,000 requests and going up to support over 250,000 requests. This flexibility makes it suitable for businesses of all sizes, ensuring consistent protection even during traffic surges.
2. Implement Email Validation and Verification
Email validation is a key step in defending against fraudulent signups. It ensures the email address provided is correctly formatted, exists, and can receive messages. With nearly 20% of email registrations containing typos, fake addresses, or other issues, this process is crucial for maintaining a clean and reliable database. By catching problematic emails early, you can prevent fraudsters from infiltrating your system.
The process typically involves two steps: users confirm their email through a one-time passcode (OTP) or a verification link, while automated systems check the email's syntax, domain, mailbox, and reputation. This layered approach blocks fake accounts while keeping the process smooth for genuine users.
Real-time validation adds another layer of security by immediately flagging errors and suggesting corrections. This ensures legitimate users don’t miss important communications while stopping bots and fraudulent attempts at the entry point. These checks happen in milliseconds, verifying details like the domain's mail exchange (MX) records and confirming the mailbox's existence using SMTP authentication.
For scalability, an integrated validation system can reconcile data from multiple sources in real time. It can block high-risk addresses outright or trigger additional verification steps when something seems suspicious.
To keep your database healthy over time, combine double opt-in methods with regular re-validation. This ensures only engaged users remain in your system, while also identifying invalid addresses and spotting new fraud patterns. Together, these measures strengthen your overall fraud prevention strategy and maintain the integrity of your platform.
3. Use CAPTCHA to Block Automated Signups
CAPTCHA, short for "Completely Automated Public Turing test to tell Computers and Humans Apart", is a powerful tool to protect your registration forms from bot attacks. By presenting challenges like identifying objects in images or solving basic puzzles, CAPTCHA creates hurdles that are simple for humans but difficult for automated scripts to overcome. This makes it an effective deterrent against credential stuffing, mass account creation, and spam registrations.
However, CAPTCHA isn't foolproof. While it's a strong first line of defense against automated spam, modern bots have evolved. With the help of machine learning and human-solving services, some bots can bypass CAPTCHA challenges up to 90% of the time. And as Kacie Cooper from WPForms points out, certain CAPTCHA versions can frustrate users with extra steps, potentially driving away legitimate signups. To strike the right balance, it's crucial to implement CAPTCHA thoughtfully, ensuring security without sacrificing user experience.
A practical approach is to integrate CAPTCHA on the frontend while verifying its token on the backend. For instance, you could use an AWS Lambda function to reject signup requests that lack a valid token. To make the process smoother, consider activating CAPTCHA only when suspicious activity is detected, rather than requiring it for every user.
"The use of an effective CAPTCHA can help to prevent automated login attempts against accounts. However, many CAPTCHA implementations have weaknesses that allow them to be solved using automated techniques or can be outsourced to services that can solve them. As such, the use of CAPTCHA should be viewed as a defense-in-depth control to make brute-force attacks more time-consuming and expensive, rather than as a preventative." - OWASP Cheat Sheet Series
For a less intrusive option, tools like Cloudflare Turnstile offer a seamless user experience by operating unobtrusively. Ultimately, CAPTCHA should be seen as one layer of a broader strategy to secure your registration process.
4. Monitor IP Reputation and Location Data
When a user registers, their IP address reveals important details like location, internet provider, and connection type. By examining this data, you can identify patterns that typical users don't usually follow - such as a surge of signups from high-risk countries or repeated registrations from the same IP in a short time frame. These insights lay the groundwork for a deeper analysis using IP reputation scoring.
IP reputation scoring assigns a risk level to each IP by cross-referencing it against fraud databases. If an IP has a history of spam, botnet activity, or fraudulent behavior, it gets a lower score. Fraudsters often rely on proxy servers and VPNs to mask their real location, which is why detecting proxies is a vital part of any fraud prevention strategy. For instance, AI-powered platforms have effectively used IP scoring based on past data to cut down on false declines.
Be on the lookout for red flags like mismatches between IP location and billing information, frequent IP changes, multiple accounts tied to a single IP, or activity originating from high-risk regions. In 2023, 13.5% of global digital account creation attempts were suspected to be fraudulent, and online payment fraud surpassed $48 billion.
To strengthen your defenses, combine IP intelligence with other security measures. For example, PayPal’s fraud detection system evaluates over 1,000 data points, including IP addresses and transaction speeds, to keep fraud rates below industry standards while ensuring smooth experiences for genuine users. Instead of outright blocking all VPN users, flagging unusual patterns for extra verification offers a balanced approach that respects user privacy without compromising security.
Real-time monitoring is another key tool. It continuously tracks IP activity and can trigger alerts within seconds if suspicious behavior is detected. Amazon’s fraud prevention system, for example, processes millions of transactions daily, automatically blocking risky logins or payments and escalating high-risk cases to investigators in less than five seconds. This kind of rapid response helps safeguard your platform while minimizing disruption for legitimate users.
5. Track Device Fingerprints for Coordinated Fraud
Device fingerprinting works by creating a unique identifier, or hash, based on a device's attributes - things like browser settings, operating system, hardware specifications, screen size, and installed plugins. This method makes it possible to identify devices even if users switch browsers, delete cookies, or use the same network. For fraudsters attempting to create multiple fake accounts on one device, fingerprinting can expose these connections.
To implement device fingerprinting, you'll need a client-side script that gathers key data points (such as user agent, screen resolution, and battery usage) and a backend API to process this data. By storing these signals on the server, you can monitor registration patterns without interfering with the user signup experience.
One of the biggest advantages of device fingerprinting is how it operates quietly in the background, improving fraud detection without causing friction during signups. It’s particularly effective against advanced fraud schemes and helps reduce false positives. Given that account takeover incidents cost consumers nearly $16 billion in 2024 - a 23% jump from the previous year - this kind of stealthy protection is becoming increasingly critical.
That said, privacy concerns are a key consideration when using device fingerprinting. Laws like GDPR, CCPA, LGPD, PIPL, and PIPA mandate transparency and user consent. To comply, ensure your implementation is clear about data usage, obtain proper consent, and strictly follow data protection guidelines. Build APIs to collect only the minimum necessary data, and offer options for privacy-conscious users to reduce potential risks.
For stronger fraud prevention, combine device fingerprinting with tools like behavioral biometrics and identity verification. This multi-layered strategy helps detect coordinated fraud while ensuring legitimate users can register without unnecessary hurdles. Such an approach enhances your defenses as you continue fine-tuning your registration processes.
6. Apply Multi-Factor Authentication for High-Risk Signups
Multi-factor authentication (MFA) adds an extra layer of security when a registration appears suspicious. Instead of applying it universally, MFA should be triggered only when risk scores flag unusual activity. When anomalies are detected, you can either challenge users with MFA or block access altogether. This approach ensures a balance between strong security and a seamless registration experience.
MFA is highly effective, preventing over 99% of automated attacks. However, synthetic identity fraud still occurs, often due to compromised one-time passwords (OTPs). That’s why selecting the right MFA method is crucial. For high-risk scenarios, prioritize phishing-resistant options like hardware security keys, biometric verification, or authenticator apps that support FIDO2/WebAuthn standards.
While security is vital, user experience (UX) cannot be overlooked. According to Transmit Security, overly complex MFA processes can frustrate users and hurt UX. To address this, consider adaptive authentication. This method adjusts security measures based on context - such as location, device, and user behavior - ensuring stricter verification is applied only when necessary. This dynamic approach maintains both security and usability.
It’s also important to recognize the vulnerabilities of OTPs. TransUnion highlights that OTPs are susceptible to hijacking through SIM swaps, call forwarding, or unauthorized number reassignments. To reduce this risk, verify phone ownership using authoritative data from direct carrier relationships before sending OTPs.
To simplify implementation, integrate authentication and fraud detection into a unified no-code platform. This allows you to customize when MFA is triggered without adding technical complexity. Additionally, it provides flexibility with options like passkeys, SMS OTPs, email magic links, or social logins, catering to both security needs and user convenience.
sbb-itb-cfbd9fd
7. Use Behavioral Analytics to Identify Fake Registrations
Behavioral analytics takes fraud detection a step further by analyzing how users interact with your platform. It monitors patterns like keystrokes, mouse movements, typing speed, and session flow to uncover suspicious behavior. For instance, actions such as filling out forms unusually fast or creating multiple accounts from the same device using different identities can signal fraudulent activity.
This method builds on traditional security measures by offering a more dynamic way to understand user behavior. AI-powered systems compare each registration attempt against typical user patterns, assigning risk scores to flag unusual behaviors. For example, rapid data entry might indicate automation. When these risk thresholds are crossed, the system can automatically deny access or prompt additional verification steps. Importantly, this all happens without creating extra hurdles for legitimate users.
One of the key advantages of behavioral analytics is its seamless integration. It operates quietly in the background, collecting data passively, so genuine users don’t encounter any disruptions during the registration process.
Machine learning plays a crucial role here, continuously adapting to new fraud tactics. By processing vast amounts of data in real time, these systems can quickly identify anomalies and even detect new types of attacks that traditional rule-based methods might overlook.
A practical example comes from Transmit Security, which showcased its Account Opening platform in October 2023. This AI-driven platform uses behavioral analytics to detect fraudulent registrations early. It flags suspicious activities like rapid data entry or multiple account creations from the same device. By analyzing micro-level interactions - such as clicks, edits, and pauses - it provides an early warning system for fraud, helping businesses tackle threats before they escalate.
8. Set Up Rate Limiting to Stop Bot Attacks
Rate limiting is a powerful way to control the number of registration attempts from a single source, helping to counter automated bot attacks. Fraudsters often use bots to create fake accounts at astonishing speeds. According to DataDome, bots can generate one fake account every three seconds, and during coordinated attacks, these networks can churn out hundreds or even thousands of accounts in just minutes.
"Attackers can create a fraudulent account every three seconds using automation, making manual detection impossible and requiring automated prevention systems." - DataDome
Once you've implemented detection measures, managing the frequency of sign-up attempts becomes just as important. Keep an eye on registration patterns tied to IP addresses, device fingerprints, and geographic locations to spot any unusual activity. For example, traffic originating from proxy services, VPNs, or anonymized networks often signals fraudulent behavior. If you notice a surge in registrations from a single IP or an unusual spike from a specific data center, rate limiting can step in to slow down or block these attempts automatically.
Modern rate-limiting systems go beyond simple static rules - they rely on real-time fraud signals to minimize disruptions for legitimate users. These systems analyze behavioral cues like how quickly forms are completed or how users navigate your site to differentiate between humans and bots. If suspicious behavior is flagged, you can introduce additional security measures like multi-factor authentication instead of outright blocking access. This approach, often called "friction-right", ensures fraudulent activities are curbed without hindering genuine users.
For large-scale implementations, rate limiting must handle data across regions efficiently while maintaining fast responses, even during high-traffic periods. The system should be capable of storing and retrieving rate limit data quickly, ensuring smooth performance under heavy loads.
9. Use Risk Scoring for Automated Fraud Detection
Risk scoring systems assign a numerical value to each registration, with higher scores signaling a greater likelihood of fraud. Powered by AI, these systems analyze hundreds of data points in real time to calculate the probability of fraudulent activity.
One of the standout advantages of risk scoring is its ability to work quietly in the background for legitimate users. It minimizes disruptions, ensuring smooth user experiences while automatically blocking bots or flagging suspicious registrations. Since bots struggle to replicate human behavior perfectly, AI systems can adapt to evolving fraud tactics over time.
These systems factor in a wide range of signals, such as login locations, device fingerprints, registration timing, form interaction patterns, and behavioral biometrics. They also cross-check identity data against reliable databases to detect anomalies. A 2023 study revealed that 59% of consumers feel more inclined to shop with a brand that implements additional security measures.
Risk scores streamline decision-making by automating the process: registrations with low risk are approved instantly, while high-risk ones may require extra verification or are blocked outright. These systems also monitor user activity continuously, enabling real-time fraud detection. Plus, they integrate seamlessly with existing tools, eliminating the need for extensive changes to your infrastructure.
"Everything in prevention needs to be in a split second, especially now, when interactions and payment transactions are often instant." - Adine Wempe-Kalff, ING Bank
10. Review Metrics and Update Registration Policies
After implementing detection methods, it's crucial to regularly evaluate your system and update policies to maintain strong fraud prevention measures.
Fraud prevention is an ongoing battle that requires constant vigilance. As fraudsters increasingly use AI to develop sophisticated tactics - like synthetic identities and deepfakes - policies that remain static can quickly become ineffective.
To keep your defenses sharp, monitor both direct fraud incidents and key system performance metrics. Pay attention to indicators such as false positive rates, detection speed, financial losses, user drop-off during verification, and overall system costs. These metrics help you strike the right balance between maintaining security and ensuring a smooth user experience.
Quick action is essential. Fraud teams should update rules daily, respond in real time, and replace static models with dynamic systems capable of adapting to new threats. These ongoing adjustments work hand-in-hand with earlier strategies like risk scoring and behavioral analytics.
Make team reviews a yearly priority. Use this time to evaluate inactive accounts, update access permissions, and discuss emerging fraud trends. Sharing insights within your organization and with industry peers can further bolster your defenses.
"The challenge lies in staying ahead of fraudsters who face no such constraints. As Wempe-Kalff from ING puts it, the future of fraud prevention may be 'AI fighting AI.'"
- Adine Wempe-Kalff, ING Bank
Comparison Table
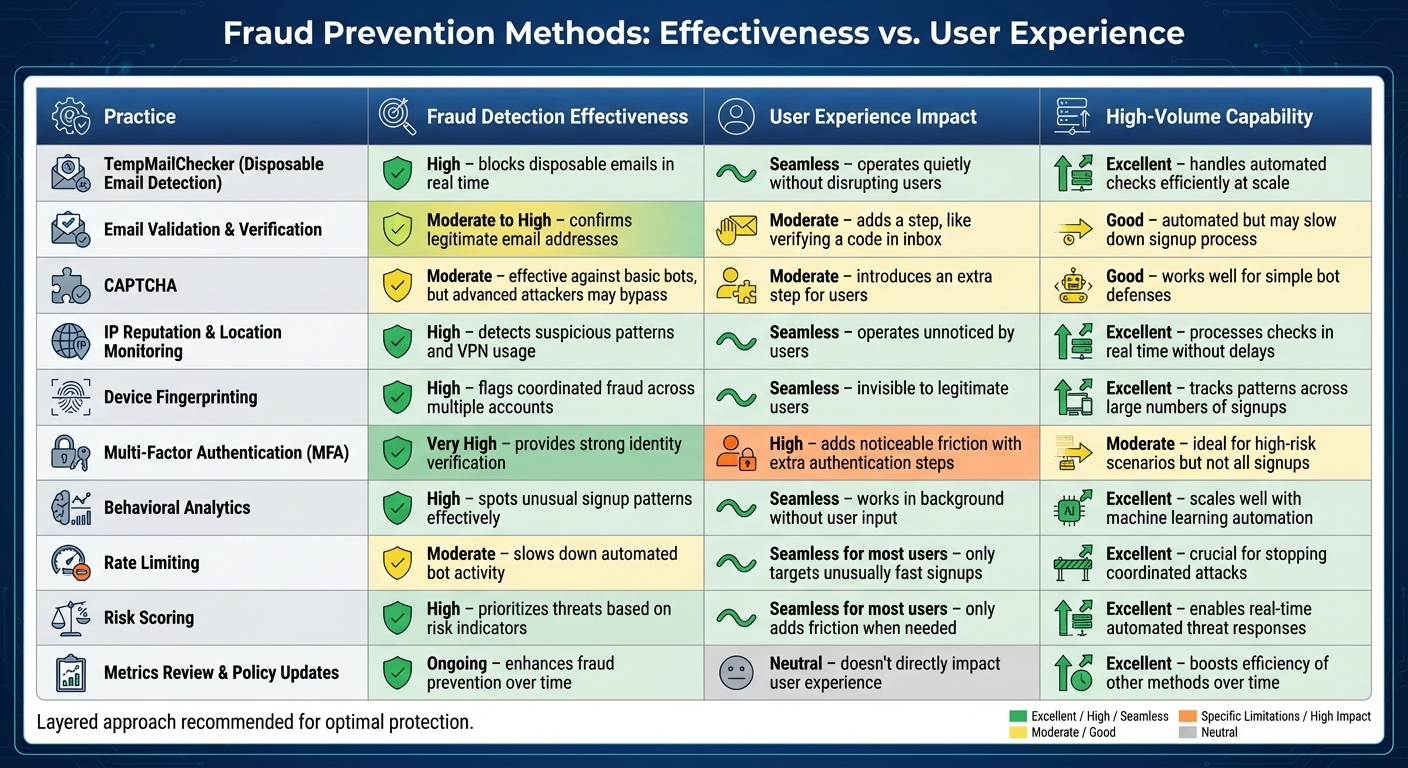
Fraud Prevention Methods Comparison: Effectiveness, User Impact, and Scalability
When deciding on fraud prevention methods, it's essential to weigh their effectiveness, user experience, and ability to handle high traffic. The table below breaks down how each method performs in these areas, emphasizing the need for strong and efficient fraud prevention measures.
| Practice | Fraud Detection Effectiveness | User Experience Impact | High-Volume Capability |
|---|---|---|---|
| TempMailChecker (Disposable Email Detection) | High – blocks disposable emails in real time | Seamless – operates quietly without disrupting users | Excellent – handles automated checks efficiently at scale |
| Email Validation & Verification | Moderate to High – confirms legitimate email addresses | Moderate – adds a step, like verifying a code in an inbox | Good – automated but may slow down the signup process |
| CAPTCHA | Moderate – effective against basic bots, but advanced attackers may bypass it | Moderate – introduces an extra step for users | Good – works well for simple bot defenses |
| IP Reputation & Location Monitoring | High – detects suspicious patterns and VPN usage | Seamless – operates unnoticed by users | Excellent – processes checks in real time without delays |
| Device Fingerprinting | High – flags coordinated fraud across multiple accounts | Seamless – invisible to legitimate users | Excellent – tracks patterns across large numbers of signups |
| Multi-Factor Authentication (MFA) | Very High – provides strong identity verification | High – adds noticeable friction with extra authentication steps | Moderate – ideal for high-risk scenarios but not all signups |
| Behavioral Analytics | High – spots unusual signup patterns effectively | Seamless – works in the background without user input | Excellent – scales well with machine learning automation |
| Rate Limiting | Moderate – slows down automated bot activity | Seamless for most users – only targets unusually fast signups | Excellent – crucial for stopping coordinated attacks |
| Risk Scoring | High – prioritizes threats based on risk indicators | Seamless for most users – only adds friction when needed | Excellent – enables real-time automated threat responses |
| Metrics Review & Policy Updates | Ongoing – enhances fraud prevention over time | Neutral – doesn’t directly impact the user experience | Excellent – boosts the efficiency of other methods over time |
This table underscores the importance of combining multiple strategies. No single method is foolproof against all types of fraud. For platforms handling high traffic, automated systems are indispensable. A layered defense - integrating background checks, behavioral analytics, and adaptive verifications - delivers strong protection without sacrificing the user experience.
Conclusion
In the first half of 2025, identity theft reports soared to 748,555, while platforms like Facebook removed over 1 billion fake accounts. These figures highlight the growing sophistication and persistence of fraud. No single solution can fully prevent these attacks, which is why layering multiple fraud prevention strategies is so critical.
One key tool in this layered approach is TempMailChecker, which effectively blocks disposable emails often used by fraudsters for automating fake registrations. By identifying temporary domains in real time, TempMailChecker makes it much harder for attackers to bypass verification processes.
The fraud landscape is constantly shifting. Traditional defenses are struggling to keep up with modern bots and AI-driven deception tactics. This makes continuous monitoring essential. Pay close attention to registration metrics - look for patterns like multiple signups from a single device, unusual geographic clusters, or sudden activity spikes. These anomalies can help you detect threats early, before they escalate. Staying ahead in this fight requires your fraud prevention methods to evolve just as fast as the tactics used by criminals.
To keep pace, regularly update your registration policies and risk assessments. The rise of AI in organized crime means fraud will only grow more complex through 2030. Your strategy must adapt just as quickly, blending automated tools with human oversight and routine policy adjustments.
Start by using TempMailChecker for disposable email detection. Then, enhance your defenses with tools like behavioral analytics, device fingerprinting, and adaptive risk scoring. Continuously monitor your results, refine your approach based on real-world data, and stay informed about new fraud trends. Fighting fraud requires constant vigilance - balancing strong security with a seamless experience for legitimate users.
FAQs
How does TempMailChecker detect and block disposable emails in real time?
TempMailChecker employs sophisticated real-time detection techniques to spot and block disposable email addresses. It evaluates the reputation of email domains, identifies known temporary email services, and cross-references against regularly updated blacklists. By using intelligent validation algorithms, it ensures that only reliable, long-term email addresses are accepted during registration. This helps safeguard your platform from fraudulent signups and ensures a more trustworthy user base.
How does behavioral analytics help detect fraudulent registrations?
Behavioral analytics is key to identifying fraudulent registrations by examining how users behave during the sign-up process. It looks for irregular patterns, such as completing forms unusually fast, performing repetitive actions from the same device, or showing behaviors that don't match those of legitimate users.
By detecting these red flags, behavioral analytics enables real-time risk evaluation, helping you act quickly to block fake accounts and safeguard your platform from fraud.
Why is it important to regularly update your registration policies to prevent fraud?
Regularly revisiting and updating your registration policies is a must - fraud tactics are always changing. Cybercriminals are quick to exploit vulnerabilities, using tools like AI and synthetic identities to outsmart outdated systems. By keeping your policies current, you can tackle new threats, patch security gaps, and keep your platform secure.
It’s not just about security, though. Staying ahead also ensures your business complies with legal and industry standards, all while protecting the trust of your users. In a digital world that’s constantly shifting, a flexible and vigilant approach to fraud prevention is essential.
