Why Disposable Emails Threaten Platform Security
Disposable emails are a growing security risk for online platforms. These temporary accounts, designed for short-term use, are exploited by bad actors to create fake accounts, abuse free trials, and launch phishing scams. Their anonymity makes them hard to trace and enables fraud at scale. Key risks include:
- Fake accounts and spam: Fraudsters use disposable emails to quickly create multiple accounts, overwhelming platforms.
- Promotion abuse: Temporary emails let users exploit free trials and promotional offers repeatedly, inflating costs and skewing metrics.
- Security vulnerabilities: These emails lack proper encryption, making them unreliable for password resets or sensitive communications.
To combat this, platforms should use real-time email verification tools, strengthen signup processes with double opt-in verification, and monitor account behavior for suspicious activity. These steps help protect against fraud and maintain platform integrity.
What Is A Disposable Email? - SecurityFirstCorp.com
What Disposable Emails Are and Why They Matter
Disposable Email Security Threats: Key Statistics and Risks
What Are Disposable Email Addresses?
Disposable email addresses - also known as one-time, burner, or ghost emails - are temporary email accounts designed for short-term use. These accounts often expire quickly, sometimes within 10 minutes, though some services allow them to remain active for hours, days, or even weeks. They provide a way to create anonymous, temporary inboxes that disappear without leaving a trace.
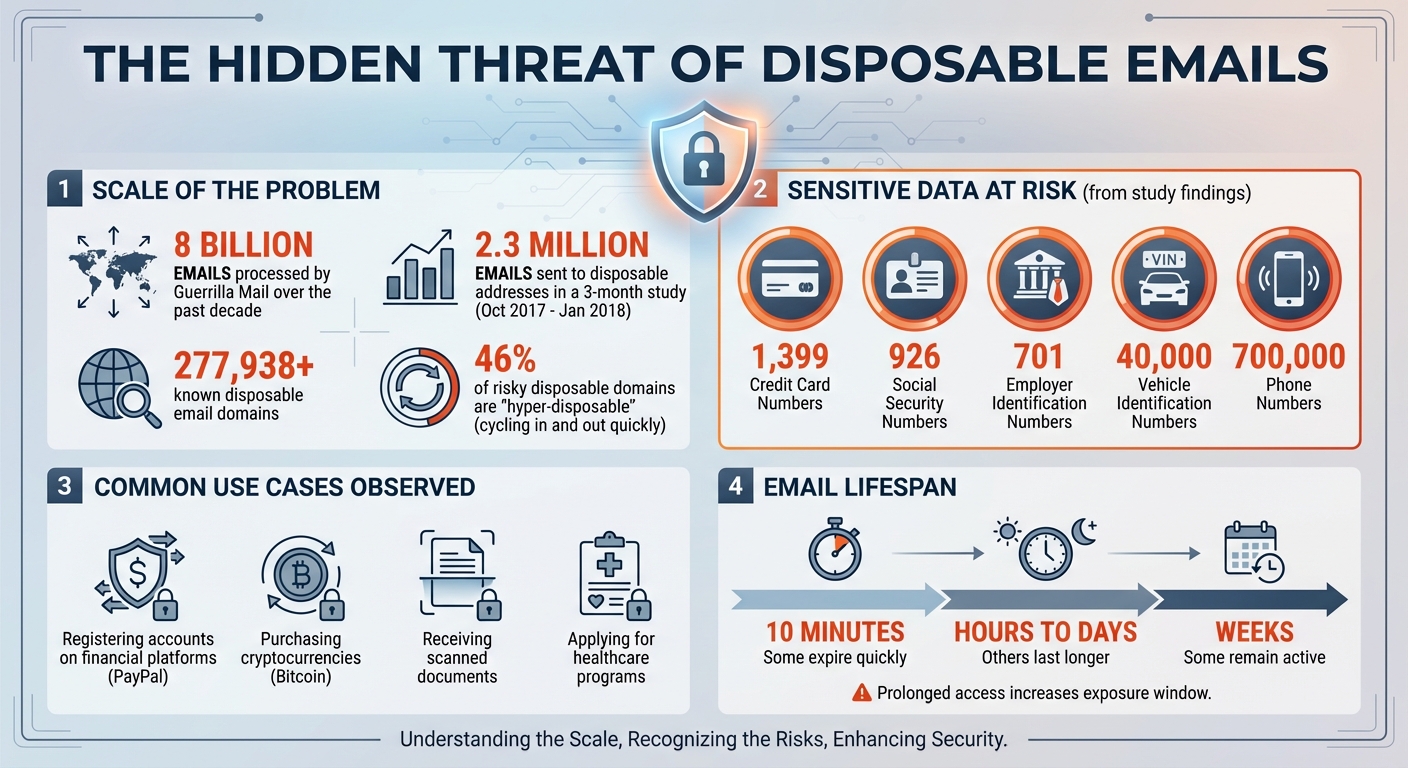
Platforms like 10 Minute Mail, Email On Deck, TempMail, and Burnermail offer users the ability to generate email addresses without requiring any personal details. To give you an idea of their scale, Guerrilla Mail has processed 8 billion emails over the past decade. During a three-month study from October 2017 to January 2018, researchers observed 2.3 million emails sent to disposable addresses. Surprisingly, these emails were used for activities such as registering accounts on financial platforms like PayPal, purchasing bitcoins, receiving scanned documents, and even applying for healthcare programs.
While these features make disposable emails convenient for quick, anonymous tasks, they also introduce serious security concerns, which we'll explore next.
Why Disposable Emails Create Security Problems
The temporary and anonymous nature of disposable emails brings a variety of security challenges. Since these accounts require little to no personal information and vanish quickly, they make user verification nearly impossible. For example, if someone uses a disposable email to create an account, platforms can’t send password resets, security alerts, or account notifications - the email address no longer exists.
This anonymity also complicates fraud investigations. Once the temporary email self-destructs, platforms lose the ability to trace fraudulent behavior back to a real person. Security measures like email verification become ineffective, allowing bad actors to exploit the system. A single fraudster could create hundreds of accounts in minutes, take advantage of promotional offers, send spam, or launch phishing attacks - all while disappearing before anyone notices.
The risks don’t stop there. A study revealed that disposable email accounts often contain sensitive information. Researchers found alarming amounts of data, including 1,399 credit card numbers, 926 Social Security Numbers, 701 Employer Identification Numbers, 40,000 Vehicle Identification Numbers, and 700,000 phone numbers. This not only puts users at risk but also exposes platforms to potential security breaches and data misuse.
How Disposable Emails Enable Fraud and Abuse
Fake Accounts and Spam
Disposable emails make it easy for fraudsters to create numerous fake accounts in no time. This layer of anonymity not only makes tracking their activities challenging but also fuels the spread of spam and scams. As a result, platforms face an increased risk of promotional abuse.
Free Trial and Promotion Abuse
Services that rely on freemium models or offer free trials are particularly vulnerable to abuse through disposable emails. Abusers exploit these systems by signing up for multiple trials or promotional offers using temporary email addresses. This endless cycle drives up platform costs, reduces genuine user engagement, and puts a strain on resources. Over time, these practices can weaken the platform's overall security and reliability.
Security Risks from Temporary Email Domains
The risks tied to disposable email domains go beyond fake accounts and promotional abuse. These temporary domains often lack strong encryption or authentication measures, making them prone to interception or unauthorized access. This limited security not only increases risks for users but also for the platforms they interact with. Additionally, the short lifespan of these emails can lead to complications, such as being locked out of accounts, losing access to password resets, two-factor authentication codes, or even important receipts once the email expires.
sbb-itb-cfbd9fd
How to Detect and Block Disposable Emails
Using Real-Time Disposable Email Detection
To tackle disposable emails effectively, consider integrating real-time email verification APIs into your signup process. These tools instantly check email addresses against an up-to-date database of disposable domains by validating syntax, DNS records, and MX records. Essentially, they ensure mailbox availability without slowing down the signup experience.
Take TempMailChecker, for example. It processes requests in under a millisecond, leveraging a daily refreshed database of over 277,938 disposable domains. The API returns a simple JSON response indicating whether an email is temporary. For those just starting out, their free tier offers 25 API requests per day - perfect for testing before full-scale implementation.
To maintain a smooth user experience, consider how you handle flagged emails. Instead of outright rejecting them, you could display a polite message requesting a permanent email address to proceed with registration. This approach balances security with user convenience.
But real-time detection is just the beginning. Strengthening your overall signup and authentication processes is key to building a robust defense.
Improving Signup and Authentication Processes
Blocking disposable emails at signup is a good first step, but combining this with other security measures makes your platform even more secure. For instance, monitoring for unusual patterns - like multiple accounts created rapidly from the same IP address - can help identify coordinated abuse. Another effective measure is implementing double opt-in verification, requiring users to confirm their email address before completing registration. This step filters out temporary addresses that can’t receive confirmation emails.
You can also use infrastructure signals to spot newly created disposable domains. Tools like SPF, DKIM, DMARC, and WHOIS data can reveal suspicious activity. For example, scanning WHOIS records for recently registered domains or keywords like "temporary" can help detect disposable domains that haven’t yet made it to blocklists. By combining these signals, you can stay ahead of new threats.
Continuous Monitoring and Risk Management
Detecting disposable emails doesn’t stop at registration. Regularly revalidating email addresses helps identify accounts that switch to temporary emails or were created using disposable addresses that initially slipped through. Monitoring account behavior is equally important. Watch for signs like rapid trial signups, abuse of promotional codes, or accounts that never engage with email communications. These patterns can indicate misuse.
Adjust your fraud scoring based on these behaviors to trigger additional verification steps or closer scrutiny of transactions. Continuous monitoring is critical, especially since around 46% of risky disposable domains are "hyper-disposable", cycling in and out quickly. Relying solely on static blocklists won’t cut it. A multi-layered detection strategy combined with ongoing monitoring ensures long-term security for your platform.
Conclusion
Tackling disposable email abuse goes far beyond just keeping spam at bay - it’s about safeguarding your platform from deeper vulnerabilities. These temporary email addresses allow fraudsters to stay anonymous, slip through verification systems, and misuse your platform with fake accounts, trial exploitation, and promotional fraud. The fallout? Skewed analytics, increased server costs, compromised data integrity, and frustrated users unable to receive critical communications like password resets or security alerts. Alarmingly, past cases have shown disposable emails being used to register sensitive accounts, potentially exposing users to serious data risks.
"In short: you're trading short-term convenience for long-term consequences"
- Atomic Mail
The solution starts with real-time detection. Tools like TempMailChecker verify email addresses in less than a millisecond, leveraging a constantly updated database of over 277,938 disposable domains. But detection alone isn’t enough. Strengthen your defenses with double opt-in verification, behavioral monitoring, and ongoing revalidation. By combining these strategies, you build a comprehensive shield that not only detects threats but actively mitigates them.
FAQs
How do disposable email addresses create security risks for platforms?
Disposable email addresses bring a host of security headaches for platforms, often becoming a gateway for fraudulent activities. They make it simple for users to create fake accounts, dodge email verification, and operate under the radar - all of which can lead to system exploitation. Some of the most common problems tied to these emails include abusing free trials, taking advantage of promotions, and engaging in synthetic identity fraud.
Another challenge? These emails make it tough to track and block bad actors. Once flagged, they can easily create new accounts in no time. To safeguard your platform, it’s crucial to adopt detection strategies, keep an eye out for suspicious behavior, and leverage tools specifically designed to spot and block disposable email domains.
How can platforms identify and block disposable email addresses effectively?
To keep your platform safe from the misuse of disposable emails, start by using email verification APIs that can spot temporary email domains instantly. Add MX record checks to confirm that email domains are valid and active. It's also a good idea to maintain an updated blacklist of known disposable email providers. On top of that, monitor user behavior to catch unusual patterns, like multiple accounts being created from a single IP address or a surge of rapid signups. These measures can help protect your platform from fraud while ensuring your users still have a seamless experience.
Why do fraudsters use disposable email addresses?
Fraudsters are drawn to disposable email addresses because they enable fast and anonymous account creation. These temporary emails allow users to sidestep verification processes, avoid detection, and remain untraceable. This layer of anonymity is frequently misused for illicit activities, such as creating fake accounts, taking advantage of free trials, and abusing promotional deals.
On top of that, disposable emails make it easier for scammers to flood platforms with spam or create malicious accounts without fear of being banned or blacklisted. Their short lifespan provides a simple way to bypass security measures, creating serious challenges for maintaining platform security and trust.
