How to Stop Promo Code Abuse with Email Validation
Promo code abuse costs businesses billions annually, but email validation can help stop it. Fraudsters exploit promotions by creating fake accounts, using disposable emails, and automating abuse with bots. These tactics inflate costs and distort metrics like customer acquisition and lifetime value.
The solution? Email validation blocks disposable emails, detects fake accounts, and ensures promotions reach real users. Techniques like syntax checks, domain verification, and disposable email detection protect your campaigns at key points like sign-up, referral, and checkout.
Key Takeaways:
- Promo code abuse costs U.S. businesses $89 billion yearly.
- Common methods include multi-accounting, referral fraud, and bot attacks.
- Email validation prevents abuse by blocking fake or temporary emails.
- Tools like TempMailChecker offer real-time detection using a database of 277,938+ disposable domains.
Common Promo Code Abuse Tactics
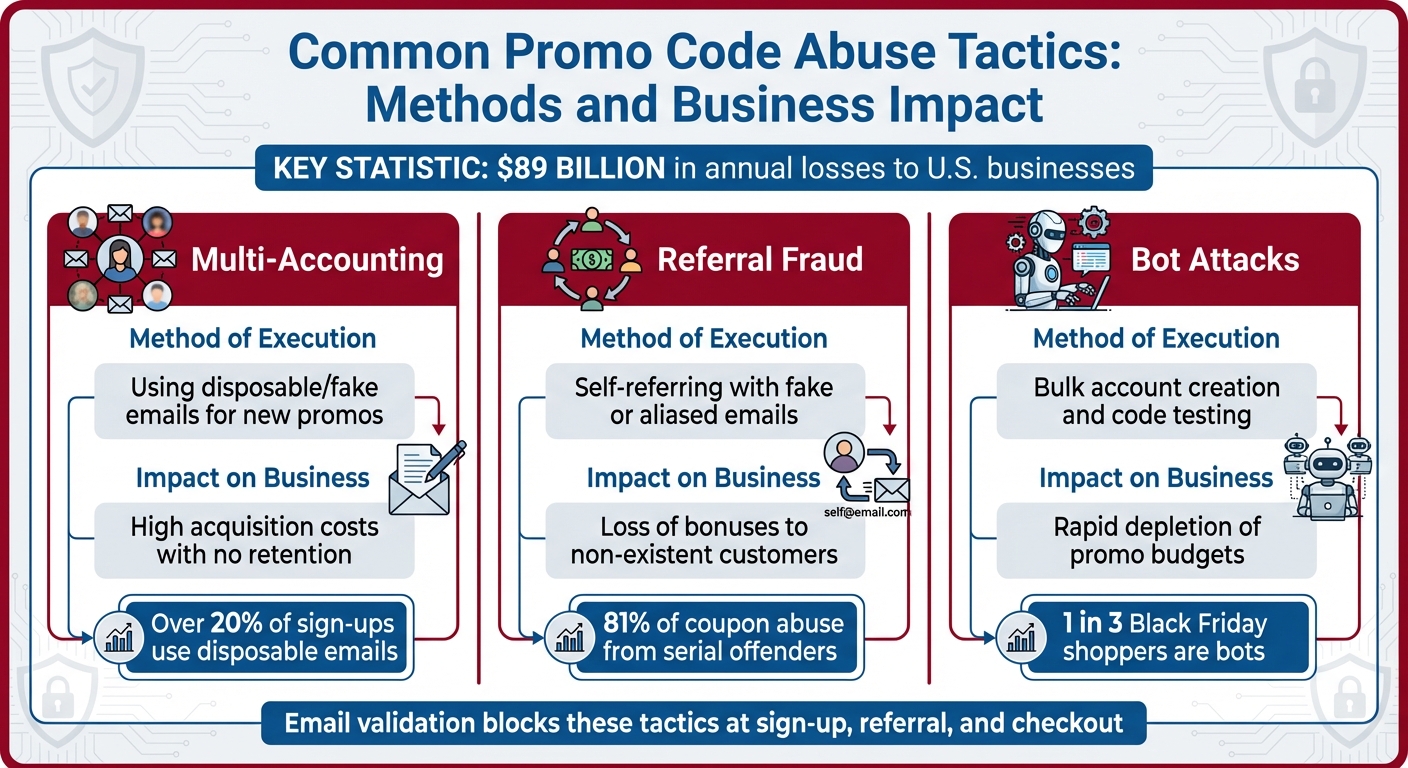
Common Promo Code Abuse Tactics: Methods and Business Impact
Understanding how fraudsters operate is the first step in stopping them. Many promo code abuse schemes rely on email-based tactics that allow bad actors to sidestep "one-per-customer" restrictions. Below, we’ll dive into some of the most common strategies fraudsters use and why strong email validation is a critical defense.
Creating Multiple Accounts with Fake Emails
One of the most frequent tactics is multi-accounting - where fraudsters create dozens, or even thousands, of fake accounts to repeatedly claim new customer discounts. They use disposable email services to generate temporary addresses in seconds, enabling them to sign up for the same promotion over and over. Additionally, they exploit email aliasing tricks (e.g., john+1@gmail.com) to create what appear to be unique addresses, even though all messages funnel back to the same inbox.
This method is highly efficient. Unlike physical coupon fraud, which requires printing and distributing fake coupons, digital abuse can be automated. Scripts can generate thousands of fake accounts in minutes, driving up your customer acquisition costs without delivering any real customer loyalty. This is exactly why robust email validation is essential - it prevents fraudsters from taking advantage of these loopholes.
Exploiting Referral and Signup Programs
Referral programs are another favorite target because they often offer high-value rewards that can be resold or converted into cash. Fraudsters create multiple fake accounts, then refer themselves to pocket bonuses from both ends.
"Promo abusers may attempt to take advantage of first-time-use discounts by creating multiple accounts using different email addresses or aliases." - Morgan Ackley, Content Strategist, Kount
Here’s how it works: fraudsters sign up, immediately refer "friends" (which are just more fake accounts they control), claim the rewards, and vanish. They rarely browse products or make legitimate purchases. This leaves businesses paying out bonuses for customers who don’t even exist. Effective email validation can stop these self-referral schemes before they drain your marketing budget.
Automated Bot Attacks
AI-powered bots represent another major challenge. These bots can mimic human browsing behavior, rotate IP addresses using VPNs, and even solve CAPTCHAs to avoid detection. Once inside, they can create bulk accounts and rapidly exploit promo codes.
Bots also target predictable promo codes, testing thousands of combinations per second. Codes like "SAVE10" or "WELCOME2025" are particularly vulnerable because they follow simple patterns. For context, an 8-character randomized code offers over 248 trillion possible combinations, while a predictable phrase can be cracked almost instantly. During high-traffic shopping events like Black Friday, research shows that more than one in three online shoppers could be bots exploiting these promotions. Email validation becomes a crucial barrier to block these automated attacks.
| Abuse Tactic | Method of Execution | Impact on Business |
|---|---|---|
| Multi-Accounting | Using disposable/fake emails for new promos | High acquisition costs with no retention |
| Referral Fraud | Self-referring with fake or aliased emails | Loss of bonuses to non-existent customers |
| Bot Attacks | Bulk account creation and code testing | Rapid depletion of promo budgets |
Building an Email Validation Strategy
Protect your platform by stopping fake accounts right at registration. Use multiple layers of email validation at critical user interaction points to strengthen your defenses.
Types of Email Validation Techniques
To combat issues like promo code abuse, a layered email validation approach is key. Here’s how different techniques work:
- Syntax Checks: These ensure email addresses follow the correct format (e.g., user@domain.com) and catch common typos or formatting errors.
- Domain and MX Record Checks: These verify that the domain exists and has valid Mail Exchange (MX) records. This blocks emails from non-existent or misconfigured domains.
- SMTP Verification: This technique pings the mail server to confirm that the specific mailbox is active - without actually sending an email.
- Disposable Email Detection: This identifies temporary "burner" emails from services like 10minutemail or Guerrillamail. Did you know that over 20% of sign-ups on some websites come from disposable email addresses? Plus, up to 22% of emails entered into online forms are either invalid or contain errors.
| Validation Layer | What It Checks | Why It Stops Abuse |
|---|---|---|
| Syntax Check | Format and typos | Prevents accidental errors and basic bot-generated strings |
| MX/DNS Lookup | Domain validity | Blocks emails from non-existent or misconfigured domains |
| Disposable Detection | Blocklisted domains | Stops users from using temporary accounts to exploit promo codes |
| SMTP Verification | Mailbox existence | Ensures a real person can receive the promo code or confirmation |
By combining these techniques, you can significantly reduce the risk of abuse. Apply them at every key interaction point for maximum protection.
Where to Apply Email Validation
Timing is everything. Start email validation at sign-up to block fake accounts before they even enter your system. Using a real-time API is especially effective - it provides immediate feedback, so if someone tries to register with a disposable email, the system can block the submission and prompt them for a valid address.
For referral programs, validate both the referrer and the referred email addresses. This stops fraudsters from gaming the system by creating fake accounts to claim bonuses on both ends.
At checkout, a final validation check before applying high-value promo codes ensures these codes are used by legitimate, long-term users - not by temporary accounts created just minutes earlier. Companies that use strong validation measures report an average 5.7% increase in deliverability rates.
Fine-tuning these applications with proven strategies can make your promo code system even more secure.
Best Practices for Blocking Fake Emails
Technical checks are essential, but combining them with best practices can ensure only legitimate users get access to promo codes. One of the strongest defenses? Double opt-in. Requiring users to click a confirmation link sent to their inbox verifies that the email address is valid and capable of receiving messages - something disposable addresses often fail to handle reliably.
"When someone uses a disposable email, it sends a clear message: I will never check this inbox in my life again." - Jakub Ziecina, Bouncer
Another effective tactic is blocking known disposable domains. Use a frequently updated database to keep up with new temporary email services, which pop up regularly. You can also implement rules to identify or normalize email aliases.
Consider this: MediaShares faced a major issue when their email service provider threatened to cancel their account due to a 12% bounce rate. By introducing thorough email verification measures, they brought their bounce rate down to nearly 0%.
Finally, don’t let your database get outdated. Clean it every 3–6 months to remove expired or inactive addresses, ensuring your system stays efficient and secure.
Using TempMailChecker to Stop Promo Code Abuse
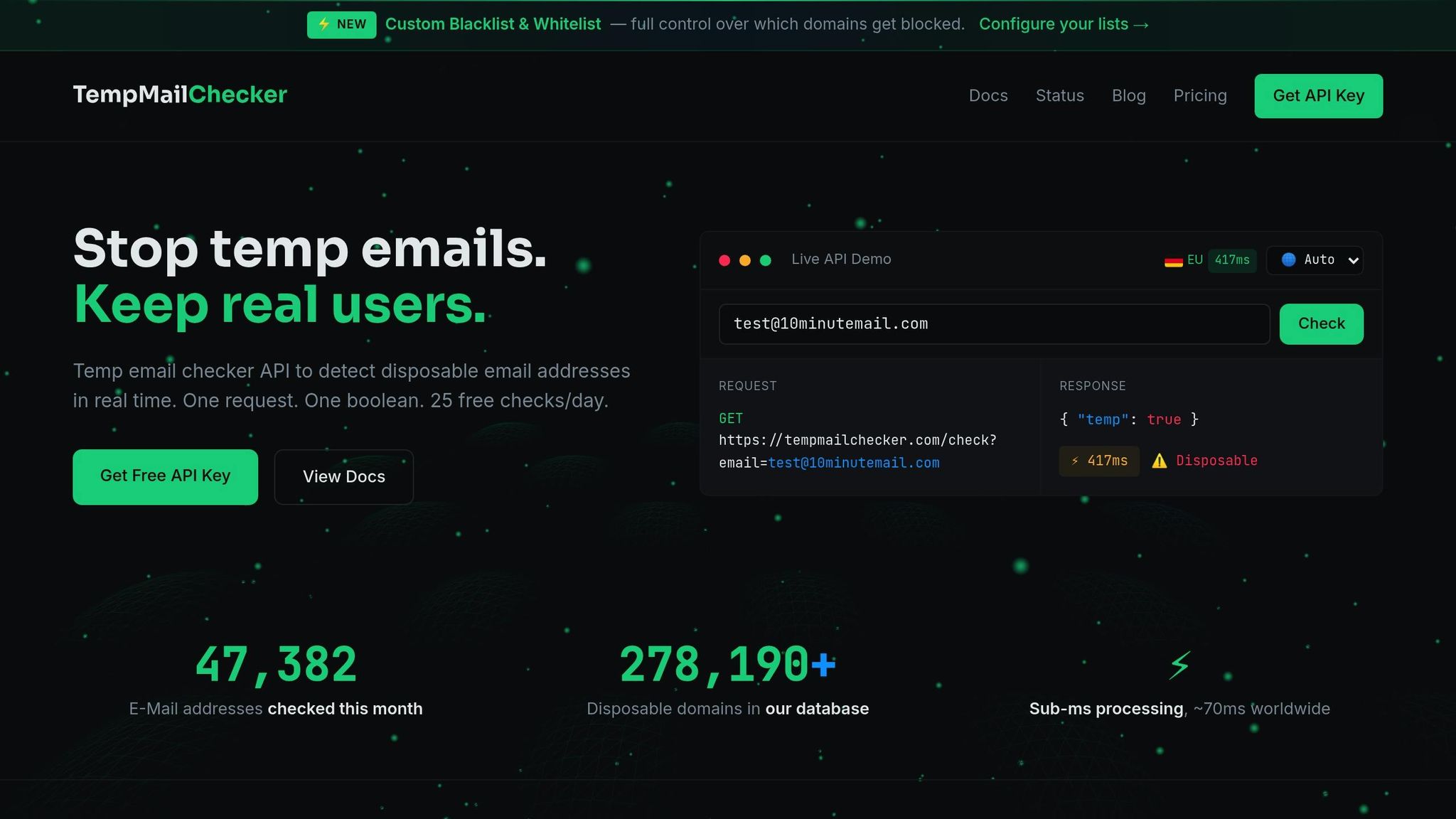
Looking to block disposable emails and prevent promo code misuse? TempMailChecker offers a real-time API that detects temporary email domains like Mailinator, GuerrillaMail, and 10MinuteMail, making it easier to safeguard your promotions.
Real-Time Disposable Email Detection
Speed matters when validating emails during signups or checkouts. TempMailChecker processes requests in under a millisecond, returning a straightforward boolean response (temp: true/false) to confirm if an email is disposable. No complicated setups or guesswork - just instant results.
The API relies on a database of over 277,938 disposable domains, updated daily to stay ahead of both well-known and emerging temporary email providers.
"If you don't block disposable emails, your signup flow will still get abused." - Tobias Jansen
This fast detection is especially critical since over 70% of AI companies report daily struggles with trial and resource abuse. With TempMailChecker, you can integrate this protection seamlessly into your promo code process.
Integrating TempMailChecker Into Your Promo Workflow
No matter your tech stack - Node.js, Python, PHP, Go, or Ruby - TempMailChecker fits right in. By validating email addresses at key stages like signups, referrals, and coupon applications, you can stop fraudsters from exploiting your system with temporary accounts. For U.S. businesses, using the dedicated regional endpoint (https://us.tempmailchecker.com/api/check) ensures minimal latency during checks.
Here’s a quick example of how to use it:
const res = await fetch("https://us.tempmailchecker.com/api/check?email=user@mailinator.com", {
headers: { "X-API-Key": API_KEY }
});
const data = await res.json();
if (data.temp) throw new Error("Blocked: disposable email address");
This validation can even be extended to monitor email changes post-signup, offering another layer of protection against abuse.
Features for U.S. Businesses
TempMailChecker is designed to meet the needs of U.S. businesses with features like reduced latency and tailored pricing options. Operating across three global regions, including the U.S., the service ensures smooth and efficient performance for domestic operations, helping you prevent spam-based promo exploitation.
The pricing plans are flexible and designed to grow with your needs:
- Free Tier: Test the integration with 100 requests per day at no cost (no credit card required).
- Starter Plan: $12/month for 3,000 requests - perfect for small-scale use.
- Growth Plan: $29/month for 15,000 requests - great for SaaS platforms and marketplaces.
- Scale Plan: $69/month for 60,000 requests, plus dedicated throughput - ideal for high-volume e-commerce businesses.
With its simple boolean response, TempMailChecker can be implemented in minutes. For added security, store your API key in environment variables, and you’re ready to block disposable emails at every critical point in your promo workflow.
sbb-itb-cfbd9fd
Monitoring and Improving Your Prevention Strategy
Email validation is a good start, but it’s not enough to stop promo code abuse on its own. To truly combat abuse, you need to consistently monitor performance and fine-tune your rules to stay ahead of evolving tactics.
Metrics to Track
Start by keeping an eye on redemption velocity - if you notice rapid and repeated redemptions from the same account, device, or location, it’s a likely sign of abuse. Another red flag is the account-to-redemption timeline; when codes are redeemed almost immediately after sign-up, it often points to automated bots.
Your true new-customer rate is one of the most important metrics to track. This tells you how many redemptions come from actual, verified individuals versus duplicate accounts using email aliases or disposable addresses. Also, look at failed redemption attempts, which can reveal how often your system successfully intercepts abuse attempts.
Don’t overlook deliverability and bounce rates, either. High bounce rates might mean you’re dealing with outdated or disposable email addresses, which can harm your sender reputation. Additionally, watch for return and refund rates on orders tied to promo codes. A spike in returns could indicate "wardrobing", where customers keep a promotional gift but return the main item.
"81% of coupon abuse stems from serial offenders - individuals who methodically exploit every available offer for personal gain." - Diarmuid Thoma, VP of Fraud and Data Strategy, AtData
With promo code abuse costing merchants an estimated $89 billion annually and 73% of retailers reporting abuse in the past year, these metrics paint a clear picture of where your resources are being drained. Use them to decide when and how to adjust your validation rules.
Testing and Updating Validation Rules
Before rolling out high-value campaigns, test your system in a staging environment by simulating fraudulent activity. This lets you identify weak points in your redemption process without risking actual revenue.
Another smart move is silent detection. Instead of outright blocking suspicious bots, monitor their behavior without tipping them off. This prevents fraudsters from adapting their bots to bypass your defenses.
"How you prevent promo abuse depends on the kind of promotion you're running, but the biggest issue is not having behavioral controls or only having basic controls in your campaigns." - Brady Harrison, Senior Data Analyst, Kount
Make sure to update your blocking rules regularly to counter new email aliasing techniques. Use behavior-based filtering tools like reCAPTCHA v3 to differentiate between real users and bots mimicking human actions. Conduct list audits every three to six months with bulk verification tools to weed out disposable or inactive addresses.
For real-time insights, set up webhook monitoring to get instant alerts about failed redemption attempts or sudden activity spikes. This lets you tweak your rules on the fly. Considering that more than one-third of online shoppers during last year’s Black Friday were fake, staying proactive is essential.
Aligning with Policies and Compliance
As you refine your rules, ensure they align with legal and operational standards. For example, your tools and processes should be GDPR compliant, respecting user preferences and safeguarding their data.
Limit the number of codes issued and cap discount volumes. Clearly display your promo policies, including redemption limits per customer and expiration dates, to establish a legal foundation for rejecting fraudulent orders.
To reduce internal risks, use role-based access controls in your promotion software. This restricts who can create, view, or edit campaigns, lowering the chances of internal misuse or unauthorized code generation. Train your marketing, development, and support teams to recognize fraud signals, maintain clean data, and follow best practices for campaign setup. These efforts create a strong first line of defense.
Finally, schedule regular list cleanings every three to six months to remove inactive, invalid, or harmful email addresses. Set up automated alerts for unusual activity, like sudden redemption spikes during off-hours or a surge in sign-ups from a single IP range. These steps ensure your anti-abuse measures not only protect your business but also meet regulatory standards.
Conclusion
Ensuring accurate email validation is a critical step in protecting your promotional campaigns from abuse. By blocking disposable and temporary email addresses at the point of entry, you can shield your marketing budget, preserve your sender reputation, and maintain clean, reliable data. Promo code abuse, which can significantly impact revenue, becomes much less of a threat when fraudsters are prevented from creating multiple accounts. In this sense, precise email validation acts as a powerful defense mechanism.
Real-time validation plays a key role here, especially when it comes to identifying fake emails. Tools like TempMailChecker offer instant detection, using a database that’s updated daily to spot throwaway addresses. Businesses that have adopted professional email verification services report impressive results - bounce rates plummet to almost zero, and deliverability scores soar to 99%.
"Validation prevents spammers from signing up on your website... Your sales and marketing teams no longer have to waste time on fake leads and spam messages." - Bouncer
For the best results, combining multiple validation methods is crucial. This includes syntax checks, MX record lookups, and disposable email detection, alongside behavioral monitoring. Regularly auditing your email list, at least twice a year, can also help keep your database clean as new temporary email services continue to emerge.
FAQs
How can email validation help stop promo code abuse?
Email validation plays a key role in preventing promo code misuse by ensuring each discount claim is tied to a legitimate, trackable email address - not a fake or disposable one. When a user enters a promo code, the system can check the email for proper syntax, confirm the domain’s existence, and compare it against a database of known temporary email providers. This helps block bots and fake accounts that try to exploit promo codes by creating multiple throwaway accounts.
Using a disposable email detection tool like TempMailChecker takes this process a step further. Its real-time API scans email addresses in milliseconds, flagging disposable domains instantly. This allows businesses to stop fraudulent signups during registration or checkout. The result? Fewer promo code abuses, more effective marketing campaigns, and better-targeted promotions that reach actual customers. Plus, it keeps your campaign data cleaner and more reliable.
How can I use email validation to prevent promo code abuse?
To combat promo code abuse, incorporating an email validation process can make a big difference. Here are the essential steps to consider:
- Syntax check: Verify that the email address is correctly formatted (e.g.,
user@example.com) to catch obvious mistakes. - Domain verification: Ensure the domain has valid DNS records, such as MX records, to confirm it can receive emails.
- Detect disposable emails: Use tools to identify and block temporary or throwaway email addresses. Services like TempMailChecker are known for their quick and reliable detection using a comprehensive database.
- Mailbox verification: For sensitive actions, validate in real-time that the mailbox exists and is capable of receiving messages.
By combining these measures, you can filter out fake or temporary emails without disrupting the experience for genuine users.
How can I integrate TempMailChecker into my system to prevent promo code abuse?
Integrating TempMailChecker into your system is a straightforward way to block disposable email addresses. Here’s how you can get started:
First, sign up for an API key on TempMailChecker and store it securely on your server. Next, incorporate a call to the TempMailChecker API into the part of your workflow where email addresses are collected - this could be on signup forms, checkout pages, or any other input fields. Once the API is called, it will return a JSON response indicating whether the email address is disposable or valid.
Use the disposable flag from the response to determine your next step. For instance, if the email is flagged as disposable, you can reject it with a polite message like, "Please provide a permanent email address to proceed." Additionally, the API supports bulk verification, which is especially helpful for cleaning up existing email lists before launching marketing campaigns.
To ensure a smooth rollout, test the integration in a staging environment before going live. By following these steps, you can safeguard your promotional offers and maintain accurate, dependable marketing data.
