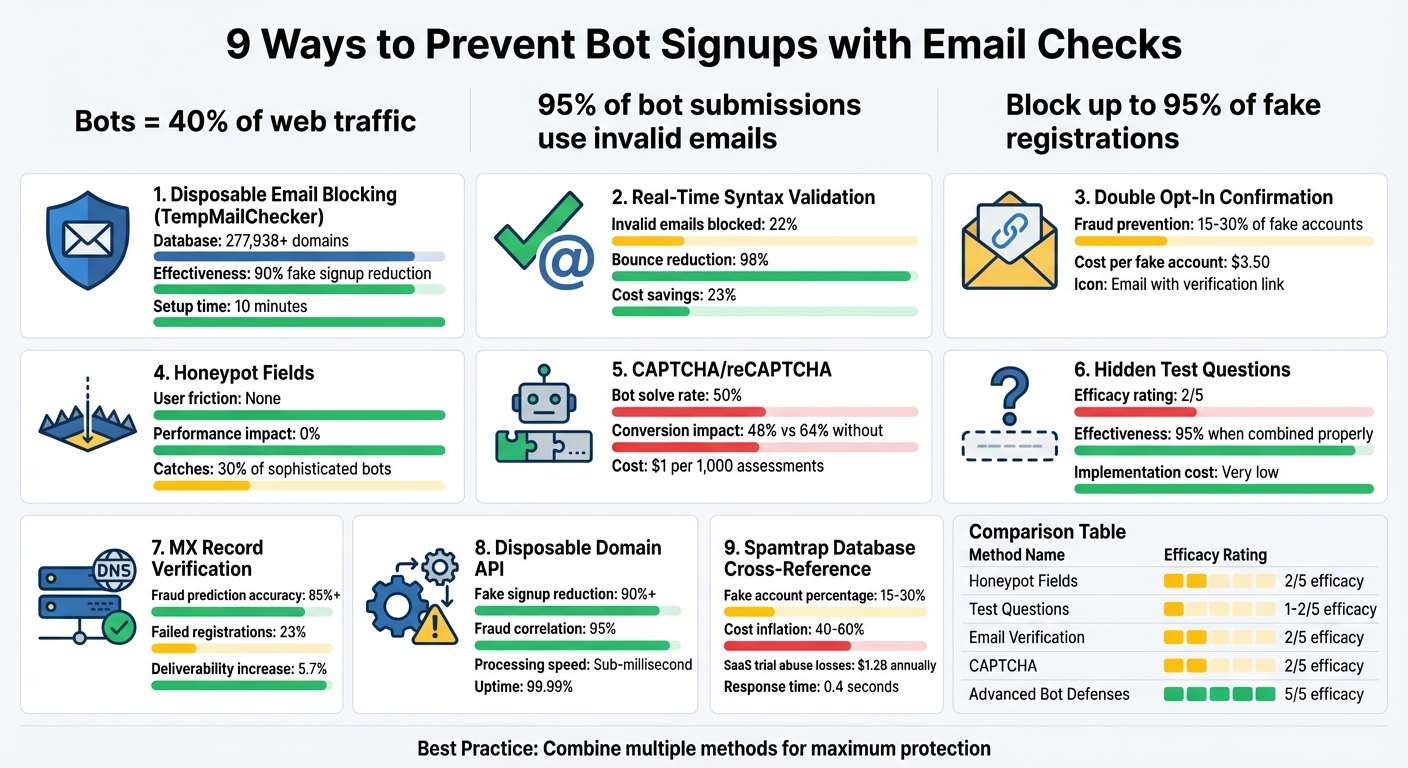
9 Ways to Prevent Bot Signups with Email Checks
Bots are responsible for over 40% of web traffic and cost businesses billions annually. Fake signups inflate user counts, skew analytics, and harm email deliverability. The solution? Email validation. Since 95% of bot submissions use invalid email addresses, email checks are one of the most effective ways to block them. Here’s how you can stop bots from infiltrating your platform:
- Block disposable emails using tools like TempMailChecker, which maintains a database of 277,938+ domains.
- Validate email syntax in real-time to catch invalid entries and reduce bounce rates by 98%.
- Require double opt-in confirmation to ensure email addresses are real and active.
- Add honeypot fields to silently trap and block bots without disrupting real users.
- Use CAPTCHA or reCAPTCHA to challenge bots while keeping the process smooth for humans.
- Include hidden test questions to detect automated scripts.
- Check MX records to verify that domains can handle email traffic.
- Integrate disposable domain blocking APIs for real-time detection of throwaway addresses.
- Cross-reference spamtrap databases to block risky or fraudulent emails.
Each method adds a layer of protection, helping you block up to 95% of fake registrations. Combining these strategies ensures a cleaner database, better email deliverability, and accurate analytics. Start simple with syntax validation and disposable email detection, and scale up with advanced tools as your needs grow.
9 Email Validation Methods to Block Bot Signups: Effectiveness Comparison
How Do You Stop Spam Bots When Even CAPTCHA Isn't Enough Anymore? (2025/625)
1. Use TempMailChecker to Detect Disposable Email Domains
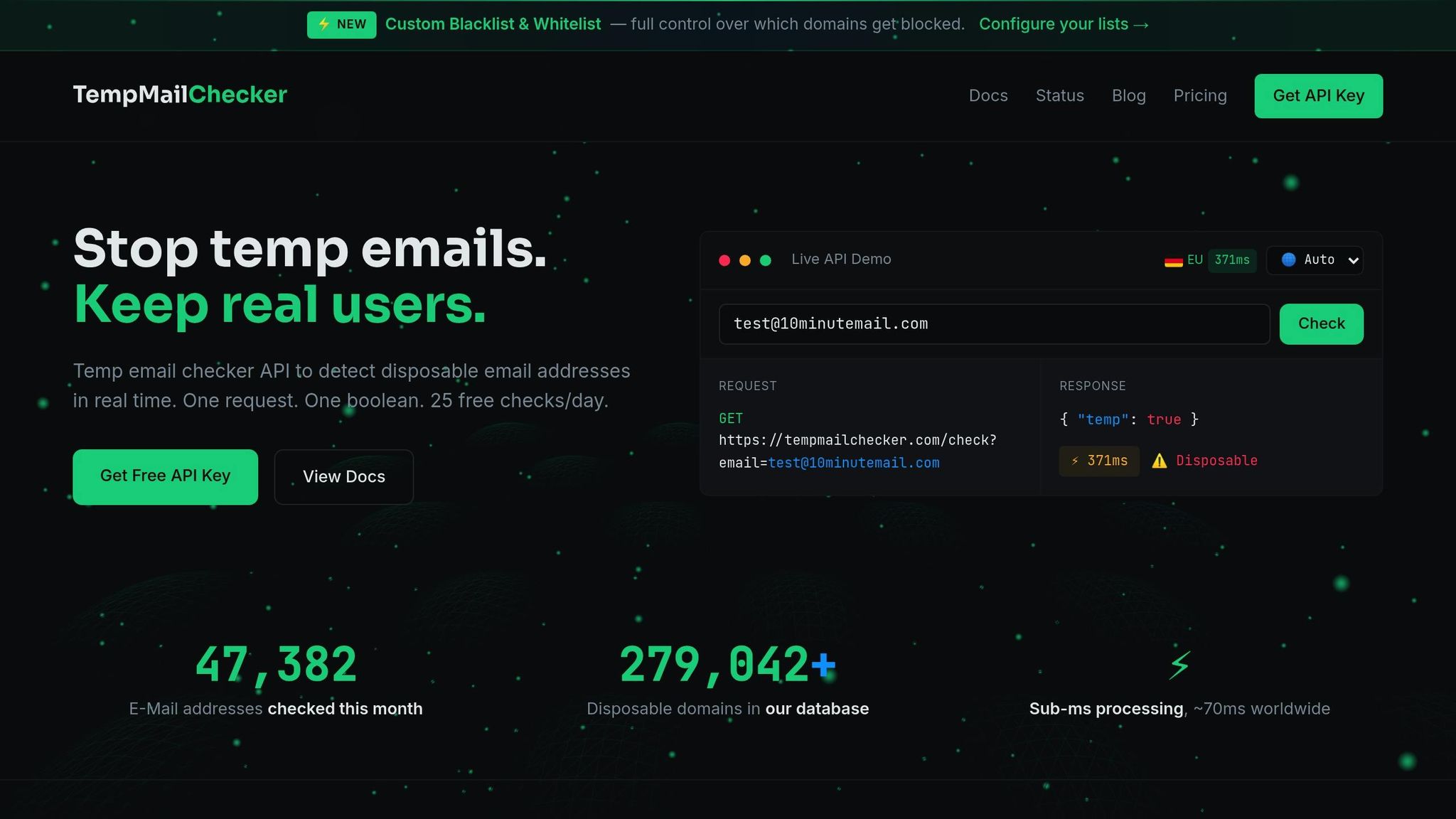
Disposable email addresses are a go-to for bots because they’re quick and easy to use. TempMailChecker combats this by maintaining a constantly updated database of over 277,938 domains to block these addresses effectively.
How It Helps Prevent Fake Signups
The impact is clear. Mike Oberman, CTO of TriviaNerd, shared his experience:
"UserCheck took 10 mins to set up and eliminated 90% of fake sign-ups. No more temporary emails getting through - we've saved countless hours and dollars by keeping our user base legitimate."
TempMailChecker’s validation process is thorough. It checks MX records, email syntax, and forwarding services. Plus, it identifies whether an email is professional, public, or role-based, making it easier to enforce specific signup rules.
Real-Time Validation in Action
TempMailChecker operates at lightning speed, processing requests in sub-millisecond times with 99.99% uptime. It handles over 100 million requests, ensuring reliability. The REST API integrates directly into your signup process with just a single call.
Thomas Petracco, Founder of UserCheck, highlights the simplicity:
"An API like UserCheck is the easiest and most reliable way to block disposable email address services without wasting time."
This real-time validation and quick integration make TempMailChecker a seamless addition to any system.
Simple Integration with Your Systems
You don’t need an entire tech team to set this up. Most teams implement the REST API in under 10 minutes. The service takes care of updating its database of disposable domains automatically, so there’s no need for manual blocklist management. It also offers native integrations with platforms like WordPress, Laravel, Zapier, and Make, making deployment even easier.
Built to Scale with Your Business
TempMailChecker isn’t just fast and easy - it’s ready to grow with you. Whether you’re a small startup or a large enterprise, it’s designed to handle your needs. The free plan includes 25 daily requests for testing, while paid plans start at $12 per month for 3,000 requests. For enterprises managing over 250,000 requests monthly, custom solutions include dedicated account management and SLA guarantees. With regional endpoints, it ensures low latency no matter where you are, all while maintaining performance even under heavy demand.
2. Validate Email Syntax in Real-Time
Stopping Bot Signups in Their Tracks
Real-time email syntax validation serves as the first line of defense against bot signups. By ensuring that every email address adheres to RFC 5322 standards - meaning it includes a local part, an "@" symbol, and a valid domain structure - you can block a surprising amount of invalid entries. In fact, up to 22% of submitted emails are invalid, with many originating from bots that rely on gibberish or predictable patterns, which fail even basic syntax checks.
This validation isn’t just about keeping junk out. It can reduce hard bounces by up to 98% and help organizations cut email marketing costs by an average of 23%. Stopping invalid data at the point of entry also keeps your email lists clean and reduces unnecessary server strain.
How Real-Time Validation Works
Real-time validation provides instant feedback, helping users catch typos immediately while preventing bots from submitting forms. However, relying solely on basic syntax checks is no longer enough. Grant Ammons, Founder of Truelist.io, explains it best:
"A simple regex check is like glancing at a street address and seeing '123 Main St.' The format looks right, but you have no idea if Main Street exists in that city... It's a surface-level check that creates a false sense of security."
The solution? A multi-layered approach. Combine client-side validation, which provides immediate feedback, with server-side checks to block bots that bypass browser-based protections. This layered strategy not only secures your forms but also strengthens your system’s overall architecture as your user base grows. Relying solely on client-side validation leaves you vulnerable - malicious scripts can easily bypass HTML5 or JavaScript-based checks.
Seamless Integration with Your Systems
Adding real-time validation to your existing systems is simpler than you might think. By using asynchronous API calls, you can keep your forms responsive - users won’t experience delays while waiting for validation results. Just make sure to store API keys securely.
One key tip: avoid making your syntax rules overly restrictive. For example, allow formats like user+tag@example.com, which many users depend on for email filtering. Additionally, prepare your system for API downtime by letting signups proceed while flagging those accounts for later verification.
This approach ensures smooth integration while maintaining scalability in high-demand scenarios.
Ready to Scale for Any Business
Whether you’re running a small startup or a large enterprise, real-time validation can scale to meet your needs. High-performance APIs can handle up to 220 transactions per second, with response times typically between 0.2 and 0.4 seconds. These services also boast over 99.99% uptime, thanks to distributed cloud data centers and auto-load balancing.
For small businesses, many providers offer freemium plans with monthly request limits, making professional-grade validation accessible without heavy investment. Larger enterprises managing high volumes can implement rate limiting and queuing systems to handle spikes in validation requests without compromising performance.
3. Require Double Opt-In Email Confirmation
Effectiveness in Preventing Bot Signups
Double opt-in adds a crucial layer of security by requiring users to verify their email addresses. After signing up, users receive a confirmation email containing a link they must click to complete the process. This step is something bots are rarely programmed to handle. Elastic Email explains the process clearly:
"The user needs to go to their inbox, open the email and click the link. It will verify that their email is real and so are they. A bot is very unlikely to do this step."
This approach not only protects your sender reputation by reducing bounce rates but also prevents your email lists from being cluttered with inactive or fake accounts. Keeping your lists clean saves money and resources, as fraudulent registrations can account for 15% to 30% of new user accounts across platforms, costing businesses an average of $3.50 per fake registration. By implementing this simple step, you lay a solid foundation for secure and efficient user management.
Ease of Integration with Existing Systems
Double opt-in is not just effective - it’s also easy to integrate into most modern systems. Many email service providers offer this feature as a built-in option, often activated with just a single toggle in your form settings. This eliminates the need for custom coding .
To ensure a smooth user experience, consider offering immediate access to lead magnets or downloads on the form’s success page, so users don’t have to wait for the confirmation email. Additionally, you can configure the confirmation "Thank You" page to automatically redirect users to their intended destination after they click the verification link. These small adjustments can help maintain user engagement while still securing your platform.
Scalability for Businesses of Varying Sizes
Double opt-in is a scalable solution that grows with your business while maintaining list quality and reducing costs in tiered pricing models . It helps prevent database bloat caused by fake accounts, but it’s important to have additional defenses in place. For instance, if bots flood your form with fake signups, sending thousands of confirmation emails to invalid addresses can harm your email deliverability and reputation.
To counter this, use tools like honeypot fields or passive CAPTCHA (e.g., reCAPTCHA v3) as a first line of defense to block bots before they trigger confirmation emails . Duncan Elder from MailerLite highlights the evolving sophistication of spambots:
"Some spambots have become more advanced and can programmatically confirm double-opt-in emails. But you should still turn on this feature since not all spam bots do this."
Monitoring your registration activity is also essential. Watch for sudden spikes in signups - like hundreds within minutes - and investigate the associated IP addresses and domains for signs of bot activity . A surge in unconfirmed signups can also indicate bot interference. Combining double opt-in with real-time syntax validation and disposable email detection can block up to 95% of fake registrations right at the point of entry.
4. Add Honeypot Fields to Signup Forms
How Honeypot Fields Work Against Bots
A honeypot field is a clever way to block bots without disrupting real users. The idea is simple: add an invisible field to your signup form. While humans won’t see it, bots scanning the HTML code will. If the field is filled out when the form is submitted, it’s a clear sign of bot activity, and the signup gets rejected.
As Audienceful explains:
"A honeypot is a form field that is invisible to humans, but not to bots. So if any data is added to the honeypot, you know it was added by a bot and the signup is rejected." (Audienceful)
The best part? Honeypots don’t interfere with user experience. Unlike CAPTCHAs, which require solving puzzles or clicking checkboxes, honeypots work quietly in the background. Elastic Email highlights this advantage:
"It's basically a behind the scenes filtering step that protects your forms without adding any additional steps for the real people trying to join your lists." (Elastic Email)
However, while honeypots are great at catching basic bots, advanced scripts can sometimes identify hidden fields by analyzing CSS or JavaScript. Because of this, honeypots are most effective as part of a broader security strategy. Let’s take a look at how easy it is to add them to your forms.
Simple Steps to Add Honeypots
Adding a honeypot field to your signup form is straightforward and requires minimal coding. Here’s how you can do it:
- Add a text field to your form, such as "honeypot" or "phone_secondary."
- Hide the field using CSS instead of the "hidden" attribute in HTML, as bots are more likely to detect the latter.
- Include an accessibility label like “Leave this field blank” to ensure compliance.
You can also configure your email service provider to automatically block or remove any signups where the honeypot field contains data. This simple addition can significantly strengthen your defenses against bots without any extra costs or impact on legitimate users.
A Scalable Solution for Any Business
Honeypots aren’t just easy to implement - they’re also highly scalable. They don’t rely on third-party services, API calls, or complex integrations, making them suitable for businesses of all sizes. Onar Alili from OOPSpam puts it succinctly:
"Honeypot is the oldest trick in the book with 0 impact on your website performance, accessibility and privacy." (Onar Alili, OOPSpam)
Whether you’re a small startup managing a handful of signups or a large enterprise handling thousands, honeypots can handle the load without additional costs or performance issues. Plus, there are no pricing tiers or API limits to worry about.
That said, honeypots alone typically catch about 30% of sophisticated bot signups. If your business is dealing with a high volume of bot traffic, combining honeypots with other methods - like disposable email detection, double opt-ins, or CAPTCHA - can offer a more comprehensive defense against both basic and advanced bots.
5. Use CAPTCHA or reCAPTCHA
Effectiveness in Preventing Bot Signups
CAPTCHA challenges are a solid first line of defense against basic automated scripts. However, bots still manage to solve around 50% of these challenges, with advanced AIs achieving an impressive 99.8% accuracy rate in cracking them. While standard CAPTCHAs can sometimes block legitimate users, specialized bot protection tools are better at minimizing false positives.
Newer versions, like reCAPTCHA v3, take a smarter approach. Instead of relying on puzzles, it uses behavioral analysis to assign a risk score between 0.0 and 1.0 in real-time. This allows you to decide whether to block, challenge, or allow a signup based on the assessed risk level. This method is particularly effective at identifying sophisticated bots while keeping the experience smooth for real users.
Ease of Integration with Existing Systems
Once you've determined CAPTCHA's effectiveness, integrating these solutions into your security system is straightforward. Tools like Google reCAPTCHA and Cloudflare Turnstile offer free tiers that are ideal for small to medium-sized businesses. For mobile applications, native SDKs for Android and iOS deliver better results than WebView implementations.
It's important to use CAPTCHA strategically. Apply it to critical endpoints - like signup and login forms - rather than every page, which could annoy users. A layered approach can be even more effective: for instance, trigger a CAPTCHA at a low rate limit and block the IP entirely if the activity exceeds a higher threshold.
Real-Time Detection and Validation Capabilities
Modern CAPTCHA solutions, such as reCAPTCHA v3 and Cloudflare Turnstile, analyze user behavior in the background, allowing for security without disrupting the user experience. However, there’s a trade-off with conversion rates. For example, a test by Animoto showed that a signup form with CAPTCHA converted at 48%, compared to 64% without one. This is why invisible CAPTCHA options are becoming more popular - they provide security without adding friction.
To ensure genuine users aren't unfairly blocked, consider offering manual verification options, such as confirmation emails. This approach balances security with usability, supporting businesses as they scale.
Scalability for Businesses of Varying Sizes
CAPTCHA solutions are designed to scale effectively, no matter the size of your business. Cloudflare Turnstile offers generous free tier limits, making it a great choice for startups. Meanwhile, Google reCAPTCHA Enterprise is priced at $1 per 1,000 assessments after the first 10,000 free monthly assessments, making it a practical option for high-traffic websites.
Matthew Murray, Director of Risk at GoFundMe, highlighted the benefits of combining CAPTCHA with other security measures:
"Combining Google's rich security expertise with GoFundMe's focus on fraud prevention is already showing promising results as we strive to keep our platform the safest place to give online."
While CAPTCHA is a powerful tool, it shouldn’t be your only line of defense. Pair it with honeypot fields, email validation, and double opt-ins to create a multi-layered security system. As your site grows and threats evolve, this combination will help protect against both simple and highly advanced bots.
sbb-itb-cfbd9fd
6. Include Hidden Test Questions or Fields
Effectiveness in Preventing Bot Signups
Adding hidden test questions to your forms can significantly strengthen your defenses against bots. These questions, like "A panda is black and ____", rely on simple logic that humans can easily answer but bots struggle with. When combined with time-based analysis - such as flagging forms completed in under 3 seconds - these measures can block up to 95% of fake signups when used correctly.
That said, there's a downside. While effective against simpler bots, these techniques have limited long-term success, with an efficacy rating of just 2 out of 5. Advanced bots are now capable of detecting and bypassing hidden fields by analyzing CSS and JavaScript. Tafara Muwandi, RVP of Data Science at F5, highlights this limitation:
"This too is effective against simple bots and is cheap and easy to implement. However, it is trivial for more sophisticated actors to engineer around and does not provide any long-term efficacy."
Ease of Integration with Existing Systems
Setting up hidden test questions is straightforward and mirrors the process for implementing basic honeypot fields. These methods require no transaction fees or complicated API integrations, keeping the cost and complexity low. To enhance their effectiveness, regularly changing field names and locations can make it harder for bot operators to create hard-coded solutions. Onar Alili, an engineer at OOPSpam, emphasizes this simplicity:
"Honeypot is the oldest trick in the book with 0 impact on your website performance, accessibility and privacy."
Real-Time Detection and Validation Capabilities
Hidden fields and test questions work in real time to validate form submissions. If a hidden field contains data or a test question is answered incorrectly, the system can block the submission immediately, preventing it from entering your database. Time-based analysis adds an extra layer of defense, as submissions completed in under 3 seconds often indicate bot activity.
Scalability for Businesses of Varying Sizes
These methods are highly scalable, handling anything from 100 to 100,000 signups per day without adding significant server load. For businesses managing multiple signup forms across regions or platforms, hidden fields and test questions are easy to replicate without introducing technical challenges.
However, as businesses grow and face more advanced threats, relying solely on these techniques becomes less effective. Studies show that basic hidden fields alone catch only about 30% of fraudulent registrations. To maintain robust defenses, it's essential to layer these methods with more advanced strategies like email verification, double opt-in processes, and CAPTCHA.
| Method | Efficacy Rating (1-5) | User Friction | Implementation Cost |
|---|---|---|---|
| Honeypot Fields | 2 | None | Very Low |
| Test Questions | 1-2 | Low | Low |
| Email Verification | 2 | Medium | Low |
| CAPTCHA | 2 | Medium/High | Low |
| Advanced Bot Defenses | 5 | Low | High |
7. Check MX Records and Email Deliverability
Effectiveness in Preventing Bot Signups
MX (Mail Exchange) records are a key indicator of whether a domain is properly set up to handle email traffic. Bots often use domains that look legitimate but lack the necessary email infrastructure. If a domain doesn’t have MX records, it’s unable to receive emails - an immediate red flag for potential fraud.
Grant Ammons, Founder of Truelist.io, highlights the shortcomings of relying solely on basic checks:
"A simple regex check is like glancing at a street address and seeing '123 Main St.' The format looks right, but you have no idea if Main Street exists in that city... It's a surface-level check that creates a false sense of security."
MX record verification fills this gap by confirming whether a domain can actually handle email. Robby Frank, Founder & CEO of 1Lookup, emphasizes:
"Domains with no MX records are a fraud signal that predicts fraud with 85%+ accuracy."
The numbers back this up: approximately 23% of new online registrations fail basic validation checks or exhibit suspicious patterns. Fake accounts cost businesses an average of $3.50 per registration in wasted resources. When combined with other validation techniques, MX record checks can block up to 95% of fake signups during registration. This method complements existing tools like syntactic checks and disposable email validations by ensuring domains are capable of real email communication.
Ease of Integration with Existing Systems
Adding MX record checks to your signup process is relatively simple. For example, PHP systems can use the built-in checkdnsrr($domain, "MX") function to verify MX records before processing signups. APIs also make this process seamless, performing the checks with a single call.
It’s crucial to perform these checks on the server side. While client-side validation offers instant feedback, server-side checks prevent bots from bypassing security by tampering with scripts. A layered validation strategy works best: Syntax Check → Domain/MX Record Check → SMTP Verification.
Real-Time Detection and Validation Capabilities
MX record checks work in real time, adding another layer of protection against bot signups. Modern email validation APIs can perform MX lookups as users fill out signup forms, typically returning results in under a second. This ensures fraudulent signups are flagged immediately without disrupting the experience for legitimate users.
For a smoother user experience, asynchronous validation is recommended. This allows checks to run in the background without freezing the page. If an API times out, the system can let the signup proceed while flagging the account for manual review later. This ensures temporary technical issues don’t block legitimate users.
Scalability for Businesses of Varying Sizes
MX record checks are highly scalable, making them suitable for businesses of any size. Whether you’re processing 100 or 100,000 signups daily, DNS lookups add minimal load to your servers and complete within milliseconds. Companies using comprehensive email validation often report a 5.7% increase in deliverability rates and a reduction in hard bounces by up to 98%.
For high-volume operations, it’s a good idea to implement rate limiting to prevent API overloading and use caching to avoid redundant checks for the same address in a short time frame. The cost of validation is also manageable - individual checks can cost as little as $0.005 per validation, and small to medium businesses typically spend between $50 and $200 per month on a mix of free tools and paid API integrations. This makes MX record validation a cost-effective and vital part of a multi-layered defense against fraudulent signups.
| Aspect | Email Validation (Syntax) | MX Record Verification |
|---|---|---|
| Purpose | Ensures the email follows proper formatting rules (e.g., "@" symbol) | Confirms the domain is configured to accept and handle email traffic |
| Process | Checks structure using regular expressions or built-in filters | Performs DNS lookups to find mail exchange servers |
| Effectiveness | High for catching typos; low for catching intentional fraud | High for catching non-existent domains and low-quality bots |
| Risk | Valid-looking emails (syntax-wise) can still be non-existent | Some disposable services use legitimate MX records to bypass this check |
8. Block Disposable Domains Through API Integration
Effectiveness in Preventing Bot Signups
When it comes to stopping bots from signing up with disposable emails, API integration proves to be a game-changer. By leveraging constantly updated databases of disposable email providers, this method reduces fake signups by over 90%. Unlike outdated static lists, APIs stay ahead by identifying new disposable email services as they appear, maintaining a 95% correlation with fraudulent activity.
Mike Oberman, CTO of TriviaNerd, shared his experience:
"UserCheck took 10 mins to set up and eliminated 90% of fake sign-ups. No more temporary emails getting through - we've saved countless hours and dollars by keeping our user base legitimate."
These APIs go beyond basic verification methods, performing multiple checks to catch even advanced bots.
Ease of Integration with Existing Systems
One of the standout benefits of these APIs is how quickly they integrate into existing systems. Most can be set up in under 10 minutes with a single REST API call. Just use your API key, parse the JSON response, and block signups when the disposable flag is true.
Take TempMailChecker, for example. It offers sub-millisecond processing and a daily updated database of over 277,938 disposable domains. With regional endpoints for low latency and support for multiple programming languages, it’s designed for speed and flexibility. The free tier, which allows 25 requests per day, provides an easy way to test the service before scaling up for production use.
For added security, consider dual validation: client-side checks provide instant user feedback for typos, while server-side validation ensures bots can’t bypass JavaScript protections. Implement asynchronous validation and cache responses to keep your signup process fast and seamless.
Real-Time Detection and Validation Capabilities
These APIs don’t just integrate easily - they also work in real time. During signup, they validate email addresses instantly, helping legitimate users fix errors while blocking disposable domains before they can infiltrate your system. Leading providers boast 99.99% uptime and handle millions of requests without slowing down performance, ensuring your signup flow remains smooth and uninterrupted.
As Robby Frank, Founder & CEO of 1Lookup, puts it:
"The best fraud prevention is invisible to legitimate users. Your validation should happen seamlessly in the background, only surfacing when action is needed."
This kind of seamless validation ensures that fraud prevention doesn’t interfere with the user experience.
Scalability for Businesses of Varying Sizes
API solutions are built to scale, whether you’re running a small project or managing enterprise-level traffic. For instance, TempMailChecker processes requests through global edge locations, offering plans from a free tier (25 requests/day) to enterprise-grade options for high-volume needs.
Here’s how API integration stacks up against other methods:
| Feature | DIY / Manual Lists | Free GitHub Lists | API Integration |
|---|---|---|---|
| Maintenance | High (Manual) | Medium (Periodic) | Low (Automated) |
| Accuracy | Low (Quickly outdated) | Moderate (Delayed) | High (Real-time) |
| Setup Time | Moderate | Moderate | Low (<10 mins) |
| Scalability | Poor | Moderate | High (Millions of reqs) |
| Additional Checks | None | None | MX, SMTP, Syntax, IP |
For businesses handling high traffic, adding rate limiting and combining email validation with IP intelligence (to detect VPNs and proxies) can further strengthen defenses. This layered approach keeps costs manageable, with hybrid validation typically costing $0.005 per check. Most small to medium businesses spend between $50 and $200 monthly to maintain robust protection.
9. Cross-Reference Emails with Spamtrap Databases
Effectiveness in Preventing Bot Signups
Spamtrap databases are a clever tool used by ISPs and blacklist providers to detect harmful activity. These databases contain email addresses intentionally placed online to identify and block illegitimate signups. By cross-referencing registration emails with spamtrap lists, you can weed out risky addresses that don’t belong to actual users. This approach can cut down on fake accounts, which often inflate user acquisition costs by 40–60%.
The numbers are alarming: fraudulent registrations make up 15–30% of all new accounts on digital platforms. Each fake account costs businesses an average of $3.50, draining resources and exposing them to fraud. For SaaS companies, the problem is even more costly, with trial abuse racking up losses of around $1.2 billion annually. Beyond financial damage, spamtrap screening protects your sender reputation. Sending emails to spamtrap addresses can lead to your domain being blacklisted by major ISPs, which means your legitimate marketing emails could end up in spam folders. This screening method not only saves money but also fits seamlessly into your current signup processes.
Ease of Integration with Existing Systems
Modern REST APIs make integrating spamtrap checks into your signup workflow a breeze - most setups take less than 10 minutes. The process is straightforward: during form submission, the system makes an API call, evaluates the response, and blocks registrations flagged with high spamtrap scores.
For optimal results, pair spamtrap checks with other validation techniques. For example, you can simultaneously run syntax checks, MX record lookups, and disposable domain screenings during form submissions. Server-side validation is also key to preventing bots from bypassing JavaScript protections. Best of all, these checks run in the background and don’t disrupt the user experience.
Real-Time Detection and Validation Capabilities
Advanced APIs offer real-time email verification, with response times averaging just 0.4 seconds. This allows you to instantly block suspicious signups and, for medium-risk email addresses, require additional verification steps like multi-factor authentication. These measures strengthen your overall bot prevention strategy. Plus, with uptime exceeding 99.99%, these services ensure your validation process won’t slow down your operations.
Real-time screening evaluates multiple factors at once, such as syntax errors, MX records, and known spam traps. It can also track domains that frequently bounce emails after initial acceptance, helping you spot emerging spam sources.
Scalability for Businesses of Varying Sizes
Once you’ve established robust real-time detection, scaling up to handle larger signup volumes is straightforward. Enterprise-level providers use distributed cloud data centers with auto-load balancing to manage heavy traffic. Standard systems can process 220 transactions per second, with the ability to scale for even higher loads. For smaller businesses, many services offer a freemium tier that includes 1,000 free requests per month, making it easy to get started.
The level of validation you choose should depend on your risk tolerance. For lower-risk activities like newsletter signups or content downloads, simple syntax checks and disposable domain blocking might be enough. However, for high-stakes scenarios like payment processing or handling sensitive data, full spamtrap screening paired with multi-factor authentication is essential.
Conclusion
Bot signups not only waste resources but also undermine the trustworthiness of platforms. To combat this, it's essential to implement a multi-layered email validation strategy that can effectively block various types of fraudulent activity. For instance, while traditional methods like CAPTCHA capture only about 30% of fake registrations, a well-rounded validation system can prevent up to 95% of fraudulent signups right at the registration stage.
A layered defense is key. Combine frontend checks, such as syntax validation, with backend tools like API verification (e.g., TempMailChecker) and behavioral analysis, including IP tracking and monitoring registration patterns. As Robby Frank, CEO of 1Lookup, explains:
"Modern fraud is sophisticated. Today's fake accounts aren't created by simple bots - they're crafted by organized fraud rings".
Fake signups cost businesses billions every year, and disposable email domains are frequently linked to fraudulent activities. This makes real-time detection a critical component of any defense strategy.
Your validation approach should align with the risks your platform faces. For lower-risk activities like newsletter signups, basic measures may be enough. However, high-risk processes require advanced tactics, such as spamtrap screening, MX record checks, and multi-factor authentication. The most effective fraud prevention systems operate seamlessly, flagging suspicious activity without disrupting legitimate users. This balance ensures both security and a smooth user experience.
Start with simple steps like frontend regex validation and a real-time email verification API. As your platform grows, enhance your defenses with additional layers, such as honeypot fields, double opt-in processes, and spamtrap cross-referencing. This scalable approach not only protects your platform but also maintains sender reputation and ensures accurate analytics.
FAQs
How does email validation help stop bot signups?
Email validation plays a key role in keeping bot signups at bay by catching and rejecting invalid or suspicious email addresses before they can be used to create accounts. It works by checking for incorrect email formats, domains that don't exist, and temporary or disposable email addresses - all red flags for automated or fraudulent activities.
By weeding out these problematic email types, businesses can cut down on fake signups, minimize spam, and safeguard their platforms from misuse, creating a safer and more trustworthy user base.
What are honeypot fields and how do they help stop bots?
Honeypot fields are a clever way to identify and block bots from submitting forms. These are hidden input fields that regular users can’t see because they’re concealed using CSS. However, bots - programmed to interact with every field - will fill them out. When the form is submitted and the honeypot field contains data, it’s a clear sign of bot activity, allowing the system to block the submission before it goes any further.
What makes this approach so effective is its simplicity. Since human users never notice or interact with the hidden field, their experience remains untouched. Meanwhile, bots unknowingly give themselves away. Honeypots are easy to set up, cost little to nothing, and can complement other tools like email validation or CAPTCHA. They add an extra layer of security without adding any hassle for legitimate users.
Why is using double opt-in important for securing email signups?
Double opt-in plays a key role in securing email signups by ensuring the email address provided is both valid and actually belongs to the person signing up. This process works by sending a confirmation link to the user's inbox, which they must click to complete their registration. It's a simple but effective way to weed out fake or bot-generated entries.
Using double opt-in helps businesses maintain cleaner email lists, cut down on spam, and guard against fraudulent signups. Plus, it builds trust with users by showing that you prioritize data security and respect their privacy.
