Complete Guide to Email Verification for SaaS Platforms
Email verification is critical for SaaS platforms to prevent fake signups, reduce fraud, and maintain email deliverability. By verifying email addresses in real-time or through batch processes, you can ensure valid, active contacts while protecting your platform from disposable emails and high bounce rates. Here's what you need to know:
- Why Email Verification Matters: Stops fake accounts, blocks disposable emails, and improves sender reputation. Even a 0.08% spam complaint rate can hurt deliverability.
- Key Methods:
- Validation: Checks proper email format.
- Verification: Confirms mailbox existence and flags risky domains.
- Confirmation: Double opt-in ensures user ownership.
- Risks Without Verification: High bounce rates, fake accounts, and delivery failures for critical emails like password resets or confirmations.
- Approaches:
- Real-Time: Validates emails during sign-up or high-risk actions.
- Batch Processing: Cleans existing lists periodically.
- Tools Like TempMailChecker: Detect disposable emails instantly, maintaining a clean user database and ensuring compliance with data laws like GDPR and CCPA.
A multi-layered strategy combining real-time checks and periodic cleanups is the best way to safeguard your SaaS platform while boosting email engagement and security.
Verify an email during user registration with Next.js 13! Mailgun and React Server Components!
Core Concepts and Challenges in Email Verification
For SaaS businesses, mastering email verification is a must for safeguarding operations and keeping communication channels reliable. Let’s break down the key concepts and challenges involved.
Email Validation vs. Verification vs. Confirmation
Though they sound similar, email validation, verification, and confirmation serve different purposes in managing email data:
- Email validation ensures the address is formatted correctly (e.g., name@domain.com), catching typos and errors right at the entry point.
- Email verification goes deeper, confirming that the mailbox exists through methods like DNS lookups and domain validation. It’s also used to flag risky addresses like disposable or catch-all domains.
- Email confirmation takes it a step further by sending a double opt-in email. This requires users to click a link, proving they own the address and agree to receive communication.
Here’s a startling fact: around 20% of email entries are either typos or outright fake. Without a confirmation step, these invalid entries can flood your subscription list, undermining your email campaigns.
Understanding these processes helps you tackle the risks outlined below.
Common Risks: Disposable Emails, Invalid Addresses, and More
Email databases degrade faster than you might think - about 2% of addresses become invalid every month, adding up to over 20% annually. On top of that, role-based addresses like info@ or support@ rarely reach individuals, and catch-all domains complicate verification by accepting any email sent their way.
A high bounce rate is another red flag. While a healthy bounce rate hovers around 2–5%, extreme cases - like 3 million invalid emails out of 5 million - can lead to bounce rates as high as 60%, damaging your domain reputation and email deliverability.
Then there are disposable email addresses. These temporary accounts disappear quickly, making follow-ups impossible and skewing your user metrics. Knowing these risks is essential for choosing the right verification approach.
Real-Time vs. Batch Verification
When it comes to email verification, you have two main options: real-time and batch methods.
- Real-time verification stops invalid emails before they enter your system. It’s perfect for lead capture forms, demo requests, webinar sign-ups, and checkout pages where accurate data is critical.
- Batch verification is used to clean up existing databases. For most databases, quarterly checks work well, but larger databases may need monthly reviews. It’s also smart to verify your list 24 hours before launching major campaigns.
The best approach? Use both methods. Real-time verification keeps new entries clean, while batch verification ensures your existing database remains in top shape. Together, they help SaaS platforms maintain strong deliverability and protect their email reputation.
Email Verification Workflow for SaaS Platforms
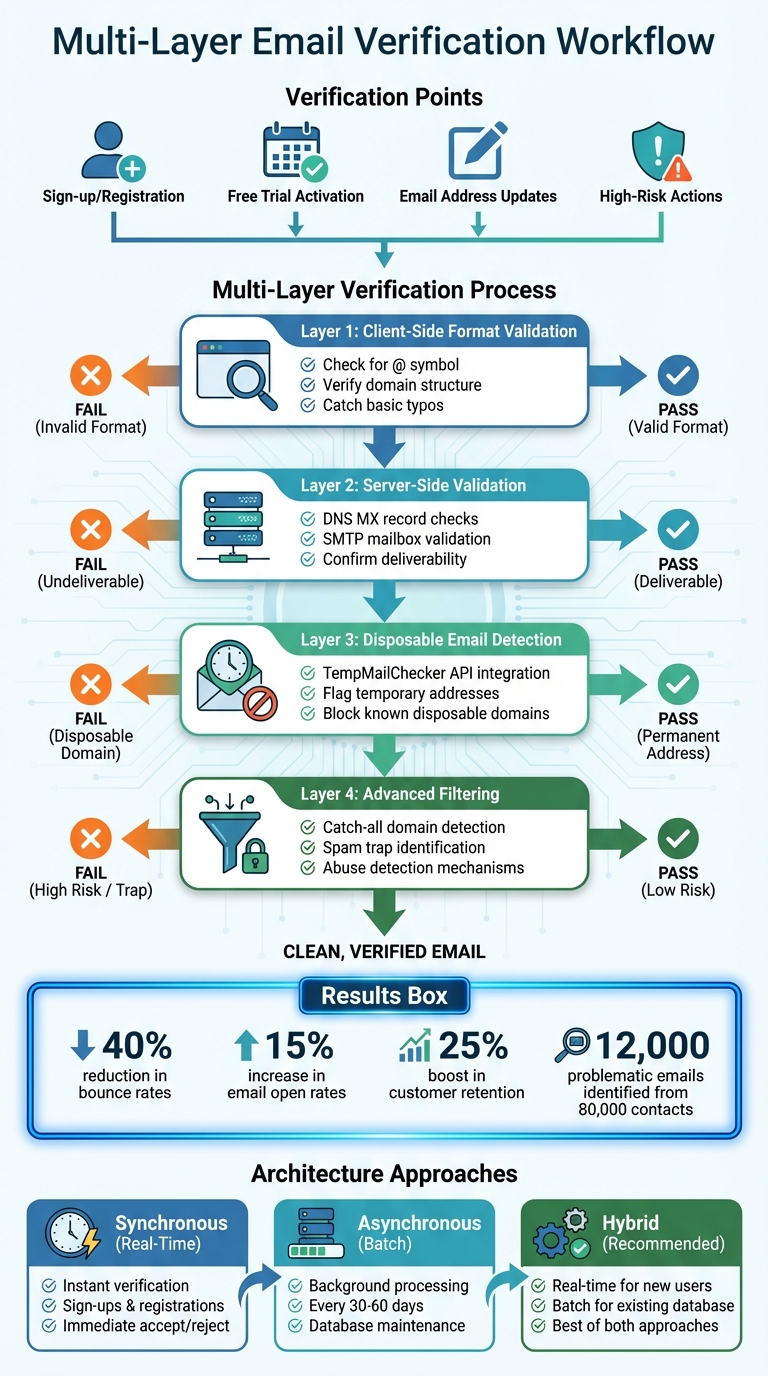
Email Verification Workflow: Multi-Layer Approach for SaaS Platforms
Creating an effective email verification workflow involves placing key checks at the right points, layering multiple defenses, and deciding whether to use real-time or batch processing based on your platform’s security requirements and tolerance for user friction. This process is crucial for maintaining user authenticity and preventing fraud.
Where to Add Email Verification in Your SaaS
Pinpoint critical user actions where email verification can reduce risks and block fraud. For instance, use real-time verification during sign-ups, free trials, or when users fill out content forms to catch invalid or temporary email addresses immediately. When users link accounts or update their email addresses, verify those new addresses to prevent account takeovers. For higher-risk activities, like posting content, you can delay verification to minimize user friction while still ensuring protection.
You can also apply conditional verification: allow leniency for trusted domains while enforcing stricter checks for domains known for disposable emails. To ensure users complete the verification process, consider locking key features or functionalities until their email is confirmed.
Multi-Layer Verification Approach
A solid verification strategy uses multiple layers to catch various types of problematic email addresses. Start with client-side format validation to check for basic issues like missing "@" symbols or incorrect domains. On the server side, perform DNS MX record checks and SMTP mailbox validation to confirm email deliverability. For detecting disposable emails, integrate tools like the TempMailChecker API. Additionally, use catch-all domain detection to flag domains that accept all emails, as these often require closer inspection. Lastly, filter out harmful addresses using spam trap and abuse detection mechanisms.
Here’s an example: A mid-sized SaaS company in the U.S. implemented a multi-layered verification system and identified over 12,000 problematic emails out of 80,000 contacts. By adding real-time API verification to their registration forms, they saw a 40% drop in bounce rates, a 15% boost in email open rates, and a 25% increase in customer retention within just 90 days.
These layers work together to ensure a clean and secure email database, but the system's architecture also plays a vital role in keeping operations smooth.
Architecture Patterns for Email Verification
When designing your verification system, choose the right architecture based on your use case. For immediate needs like sign-ups, trial registrations, or email updates, inline synchronous verification is ideal. This method verifies addresses in real time, either accepting or rejecting them instantly. For large-scale tasks like bulk imports or routine database maintenance, asynchronous batch processing works better. This approach queues email addresses for verification and updates the database in the background every 30 to 60 days, removing undeliverable, disposable, or role-based addresses, as well as fixing syntax errors.
For platforms with high traffic, a hybrid approach can strike the right balance. Use synchronous verification for new sign-ups to ensure immediate protection, while asynchronous processing keeps your existing database clean over time. This combination not only improves database hygiene but also strengthens your platform’s overall security.
sbb-itb-cfbd9fd
How to Integrate TempMailChecker
Integrating TempMailChecker into your system is a straightforward process that helps reduce fraudulent signups and ensures better email deliverability. The API provides a simple JSON response indicating whether an email address is disposable, allowing you to seamlessly incorporate verification into your existing workflows. Plus, it works in real-time without compromising the user experience.
Common Integration Patterns
Start by cleaning and standardizing the email address before sending it to the API. This includes trimming whitespace, converting the address to lowercase, and validating its basic syntax. Once prepared, make an HTTP GET request to the TempMailChecker API endpoint, passing the email address as a parameter. The API will return a JSON object with an is_disposable boolean field. Use this response to either accept legitimate emails or reject disposable ones with a clear error message.
To ensure smooth operation, implement error handling for scenarios like timeouts, API rate limits, or unexpected responses. For production environments, store your API key securely - such as in environment variables - rather than embedding it directly in your code.
Now, let’s explore how to implement TempMailChecker in PHP, Node.js, and Python.
PHP Integration
In PHP, you can use tools like cURL or the Guzzle HTTP client to interact with the API. Create a function that takes an email address, sends a GET request to https://api.tempmailchecker.com/v1/check/{email} with your API key in the Authorization header, and returns the result.
- For Laravel, encapsulate this logic in a validation rule or a service class that can be injected into your controllers. You can also create middleware to automatically verify emails during user registration.
- In Symfony, build a constraint validator that works with the framework's validation component. This allows you to use
@TempMailCheckerannotations directly on your User entity properties for streamlined integration.
Node.js and Python Integration
In Node.js, you can use the built-in fetch API or a library like Axios to connect to TempMailChecker. For Express applications, write middleware that checks email addresses during registration. If the email is valid, the request proceeds; if not, return a 400 error with a message like "Disposable email addresses are not allowed." This keeps your verification logic centralized and easy to manage.
For Python, the requests library works well for API calls. In Django, you can create a validator function and add it to the email field of your User model. Alternatively, you can define a form clean method to validate emails during form submission. In Flask, you can write a decorator function to verify emails before executing your registration route. Both Django and Flask also support asynchronous operations, allowing you to handle verification without slowing down the user experience.
These examples demonstrate how TempMailChecker can be integrated into various programming environments to ensure reliable email validation.
Best Practices for Email Verification in SaaS
Once you've established verification workflows and integration models, it's time to focus on best practices that strengthen email security and ensure compliance.
Maintaining List Hygiene and Deliverability
Email lists naturally degrade over time - about 2% each month - which means over 20% of addresses could become invalid within a year. This happens when users change jobs, abandon old email accounts, or switch providers. The solution? Verify emails as they're captured and clean your list regularly.
Make email verification a standard part of your campaign preparation, especially within 24 hours of launching major campaigns. Immediately remove addresses marked as "Undeliverable" or "Disposable". For "Accept-All" or "Unknown" addresses, segment them for follow-up verification.
Bounce rates are another critical factor. While the industry average is 2–5%, allowing your bounce rate to climb as high as 60% could result in your domain being blacklisted. Keeping your email list clean not only protects your domain reputation but also ensures reliable deliverability.
These practices also play a key role in preventing fraud.
Fraud Prevention Strategies
Did you know that 20% of users provide fake emails, and typos occur in another 20% of entries? Real-time verification during sign-ups can help catch these issues before they disrupt your system. Set up your system to flag and reject suspicious email patterns at registration.
Blocking disposable email addresses at sign-up is another effective tactic, especially to prevent abuse of free trial offers. For sensitive actions like password resets or payment updates, require users to re-confirm their email addresses.
These steps not only enhance security but also align with regulatory requirements.
Regulatory Compliance and Data Protection
Non-compliance with regulations like GDPR and CCPA can lead to hefty penalties - up to €20 million or 4% of global turnover for GDPR violations, and $7,500 per violation under CCPA. To avoid these risks, your email verification process must adhere to clear consent protocols and transparent data handling practices.
"Email compliance refers to the policies, processes, and technologies that ensure your organization's email communications follow applicable laws, industry regulations, and internal security requirements. That includes how data is handled, stored, and disclosed. It even relates to how employee email signatures and disclaimers are applied." - Exclaimer
Implement double opt-in workflows to obtain explicit consent and maintain accurate subscription records. Only collect the minimum email data necessary for verification, and give users control over their data by allowing easy access, corrections, or deletions. Opt for verification tools like TempMailChecker, which prioritize compliance with global data laws and secure data transmission.
To stay ahead, audit your email communications regularly and train your team on best practices for data protection. Keeping up with regulatory updates ensures you remain compliant as laws evolve.
Conclusion
Email verification plays a key role in creating a secure application environment and actively protecting against fraud. Without it, SaaS platforms risk fake signups and fraudulent accounts. In B2B and multi-tenant setups, the risks are even greater - one compromised account could expose sensitive business data and impact multiple users.
As discussed, your verification workflow - whether real-time or batch - serves as the backbone of your platform's security. Adding real-time verification during sign-up, regularly cleaning your email lists, and blocking disposable addresses are simple yet effective steps. These practices not only protect your sender reputation but also boost email deliverability and improve user experience throughout the customer lifecycle, from lead generation to re-engagement.
For a multi-layered approach, TempMailChecker provides sub-millisecond processing, a comprehensive disposable domain database, and easy API integration for PHP, Node.js, and Python. Whether you're using the free tier with 25 daily requests or managing enterprise-level traffic, these tools help you identify and block threats before they infiltrate your system.
By combining these practices, your email verification system doesn't just prevent fraud - it also ensures compliance. Verifying emails at the point of capture, maintaining clean lists, and adhering to GDPR and CCPA guidelines build trust with legitimate users and keep your platform running efficiently.
Start with the basics, add more layers as your needs grow, and keep refining your strategy. The strength of your email verification system depends on the actions you take today.
FAQs
What’s the difference between email validation, verification, and confirmation?
Email validation checks if an email address is formatted properly - think of it as ensuring the address includes an '@' symbol and a domain name. Verification takes it further by confirming that the email address is real and capable of receiving messages. Lastly, confirmation involves sending an email with a link or code that the user must interact with, proving they actually have access to the email account.
These steps work together to help maintain the integrity and security of your platform's user base.
What’s the best way for SaaS platforms to use real-time and batch email verification?
To ensure email addresses are accurate and valid, SaaS platforms can implement real-time email verification during sign-ups or form submissions. This method uses API calls to immediately check the email's format, verify the domain, and confirm the mailbox exists. This way, only valid email addresses make it through the system.
For maintaining long-term accuracy, platforms can rely on batch email verification. This approach involves periodically cleaning up email lists by removing invalid or outdated addresses and updating the records. It’s an effective way to keep email lists in good shape and improve deliverability.
By using both real-time and batch verification, platforms can cut down on fraud, lower bounce rates, and ensure smoother communication with users. This combination helps foster better engagement and builds trust through reliable interactions.
How can SaaS platforms ensure email verification complies with GDPR and CCPA regulations?
To align with GDPR and CCPA requirements during email verification, SaaS platforms should prioritize a few important practices:
- Secure explicit consent from users before collecting or verifying their email addresses.
- Maintain detailed records of consent to demonstrate compliance and accountability.
- Implement robust encryption and other security protocols to safeguard email data.
- Offer users straightforward opt-out options for data collection to respect their preferences.
- Conduct regular audits of your email verification processes to stay compliant with regulatory updates.
These steps not only help you adhere to regulations but also build user confidence and protect your business from legal risks.
